Whether you’re part of a global business or offshore your data operations, you’re probably familiar with cross-border data-sharing projects. These projects often result from the need of your global business to:
If you’re looking for a safe method to move data between countries while following global data regulations and safeguarding sensitive information, this guide is for you. It includes everything you must learn about transferring data across borders, from grasping regulatory needs to developing customized compliance approaches.
Whether you're in banking, manufacturing, insurance, transportation, or any industry dealing with international data transfer, our guide will light the way through the compliance maze. Let's dive into the details of cross-border data transfers.
-
Transfer customer data between oversee departments, but the data is locked.
- Use the cloud to store data or use third-party services to do analysis, enrichment, or any other data-related work that requires sharing sensitive information.
-
Compliance with data residency laws: You must ensure that your data-sharing practices adhere to the regulatory requirements of each jurisdiction where data is stored or accessed.
-
Slow or delayed data access time: You should have efficient and timely access to data across borders. When your data falls under different data residency laws, compliance checks can become a serious bottleneck to timely access data.
- Issues with retaining the analytical value of the shared data: You must ensure that data shared across borders is of good quality. This includes statistical significance, accuracy, and consistency, so it’s actually useful for analytics and decision-making purposes.
If you’re looking for a safe method to move data between countries while following global data regulations and safeguarding sensitive information, this guide is for you. It includes everything you must learn about transferring data across borders, from grasping regulatory needs to developing customized compliance approaches.
Whether you're in banking, manufacturing, insurance, transportation, or any industry dealing with international data transfer, our guide will light the way through the compliance maze. Let's dive into the details of cross-border data transfers.
Understanding Cross-Border Data Transfer
Moving data across borders has consistently gained momentum in recent decades. This trend is mainly fueled by technological advancements, globalization, and the digital economy. Let's delve into the significance of this trend and explore why it's more crucial now than ever.
Cross-border data transfer refers to physically or virtually moving data from one country to another. This includes transferring personal information, financial data, or digital content across international borders.
The scope of cross-border data transfer extends to various industries, from banking and manufacturing to insurance and transportation, where data exchange is key for operational efficiency and business initiatives.
Cross-border data transfer has always been a big part of global businesses' operations. Common activities included outsourcing and offshoring so companies could optimize processes and reduce organizational costs.
Lately, these types of projects become even more crucial. The three reasons stand out:
As a result, moving data securely across borders has become important to stay competitive and keep up with innovation. If a project that involves cross-border data sharing is around the corner in your company, keep reading, and you’ll learn how to safeguard data while maximizing its analytical value.
But first, let’s talk about challenges.
When embarking on projects involving international data transfers, your business needs to follow the laws of both your home country and the country you are sending data to, which makes these projects complex.
What is Cross-border Data Transfer: Simple Definition
Cross-border data transfer refers to physically or virtually moving data from one country to another. This includes transferring personal information, financial data, or digital content across international borders.
The scope of cross-border data transfer extends to various industries, from banking and manufacturing to insurance and transportation, where data exchange is key for operational efficiency and business initiatives.
Why is This Topic Growing in Importance in Global Business Operations?
Cross-border data transfer has always been a big part of global businesses' operations. Common activities included outsourcing and offshoring so companies could optimize processes and reduce organizational costs.
Lately, these types of projects become even more crucial. The three reasons stand out:
-
New data privacy and security rules are popping up worldwide. Laws like the GDPR in Europe, which came into effect on May 25, 2018, the Chinese Personal Information Protection Law (PIPL), which entered into effect on November 1, 2021, and Saudi Arabia's 2021 privacy law, which has been in force since 14 September 2023, are just a few examples. These laws require companies to pay closer attention to how they move personal data across borders and safeguard it regardless of its destination. Failure to adhere to these regulations can result in significant fines and damage to a company's reputation.
-
The world is more connected than ever before. Businesses rely on digital technology and global supply chains to keep things moving smoothly. (Almost) everything is in the cloud, which makes data accessible but adds another layer of complexity as every jurisdiction has a different approach to where and how the data should be stored.
- Every year, AI’s rising popularity highlights the importance of cross-border collaboration for AI systems. Access to diverse and top-notch data is key for AI systems to make them less biased and more democratic. However, global businesses must remember that to benefit from AI, they must establish compatible regulatory approaches that support the smooth flow of data while complying with regulations.
As a result, moving data securely across borders has become important to stay competitive and keep up with innovation. If a project that involves cross-border data sharing is around the corner in your company, keep reading, and you’ll learn how to safeguard data while maximizing its analytical value.
But first, let’s talk about challenges.
Challenges Associated with Cross-Border Data Transfer
When embarking on projects involving international data transfers, your business needs to follow the laws of both your home country and the country you are sending data to, which makes these projects complex.
Cross-border data projects are indeed tricky. Take the General Data Protection Regulation (GDPR), for instance. This regulation has been active since 2018, and it took companies years to grasp and adhere to its rules.
Consider that your business wants to transfer data to a country like China, the U.S., or India, where different laws were implemented at different times. Before initiating any transfer, you must be well-prepared for the specific laws of each jurisdiction.
Consider that your business wants to transfer data to a country like China, the U.S., or India, where different laws were implemented at different times. Before initiating any transfer, you must be well-prepared for the specific laws of each jurisdiction.
Your global business must begin with thorough research, meticulous planning, investment, and a continuous commitment to following data protection regulations.
Let’s share an example.
The U.S. branch of a global healthcare company wants to do a cross-border project with an Indian branch. Transferring data between the United States and India can be tricky because of:
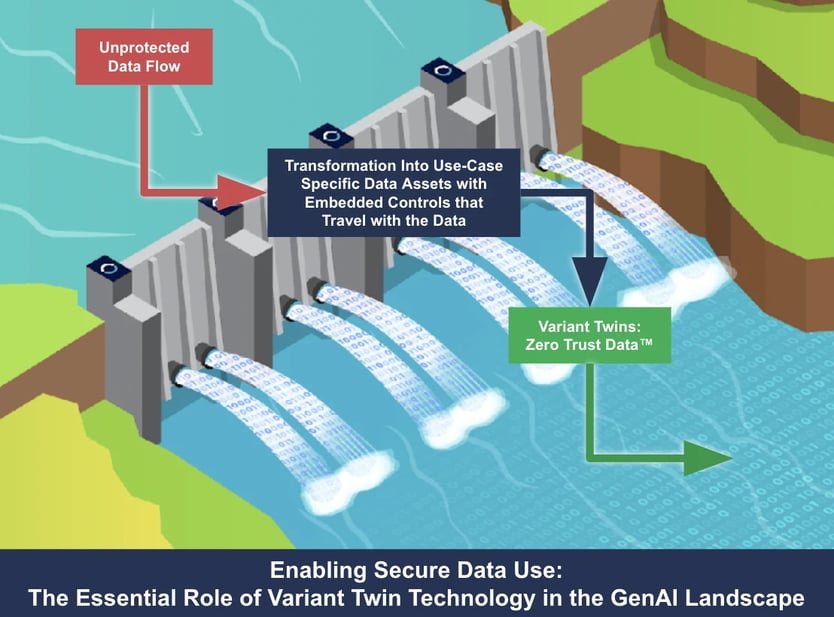
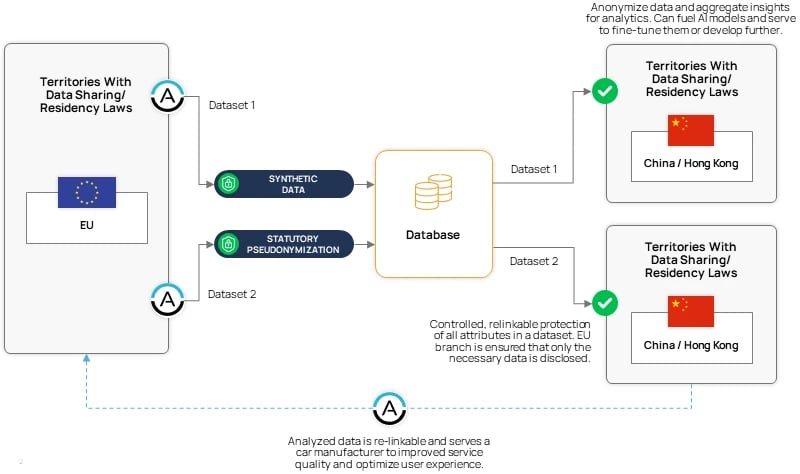
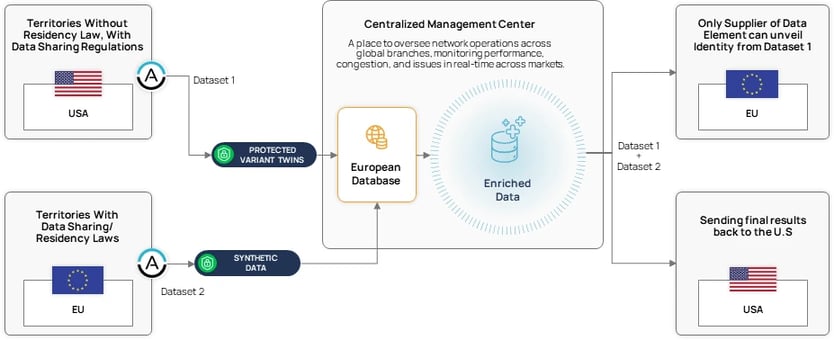
We can depict the ongoing business battle between safeguarding data and keeping its analytical features in the following way you can see below.
Let’s share an example.
The U.S. branch of a global healthcare company wants to do a cross-border project with an Indian branch. Transferring data between the United States and India can be tricky because of:
-
Legal and regulatory differences: The U.S. can operate under laws like the Health Insurance Portability and Accountability Act (HIPAA) and the California Consumer Privacy Act (CCPA). At the same time, India follows principles outlined in the Information Technology Act and the Personal Data Protection Bill.
-
Data localization requirements: India has proposed requirements mandating that certain categories of sensitive personal data must be stored and processed within the country's borders. This would require setting up a cloud in India, which bears costs.
-
Cultural and language differences: Cross-border operations often involve diverse cultural and linguistic contexts. Communicating effectively between teams in the U.S. and India requires sensitivity to cultural differences.
-
Security measures: The DPDP Act states that you should follow “reasonable security safeguards to prevent a personal data breach” if you’re sending proprietary data to India. That means implementing robust data protection so all the sensitive customer information stays safe is necessary. The best approach you can take is to choose privacy-enhancing technologies that would protect data while safeguarding its quality. The exact final combination will depend on your use case.
- Operational Challenges: Coordinating cross-border data transfer processes involves overcoming logistical and operational challenges. Differences in time zones, infrastructure capabilities, and operational practices between the U.S. and India may impact the efficiency and timeliness of data transfer operations.
We can depict the ongoing business battle between safeguarding data and keeping its analytical features in the following way you can see below.
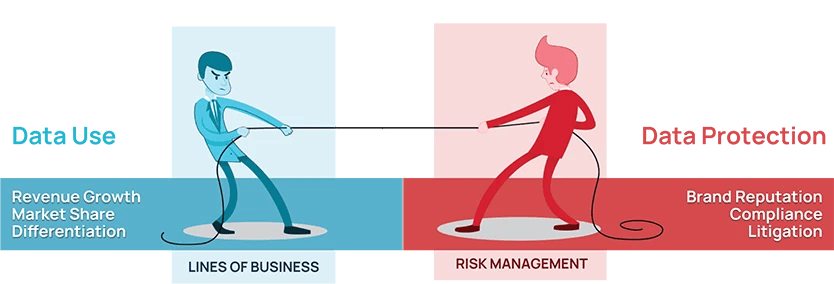
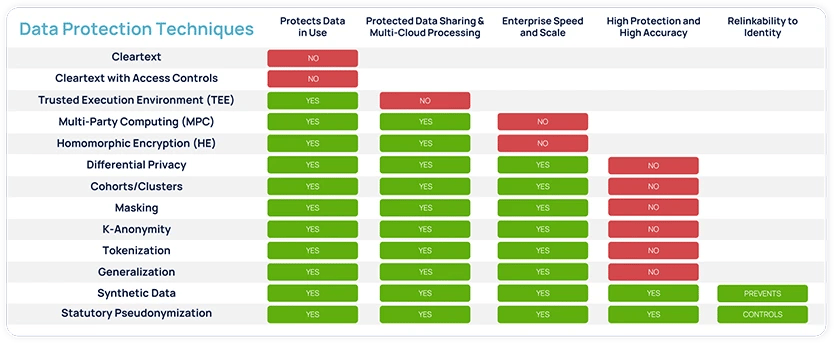
To tackle these hurdles, your organization must blend data protection technologies and legal safeguards while maintaining data usefulness.
Even if your confidential data faces the threat of misuse or theft, it must remain shielded. This ensures that no personal details are compromised, yet the data's analytical value remains intact for business teams.
Even if your confidential data faces the threat of misuse or theft, it must remain shielded. This ensures that no personal details are compromised, yet the data's analytical value remains intact for business teams.
Cross-Border Data Transfer: Understanding Regulatory Landscape
Now, let’s explore the most essential data protection laws so you can get a grasp of how each jurisdiction can impact your business.
Cross-border data transfer projects under GDPR cover moving or sharing personal data within the European Economic Area (EEA) and to another jurisdiction outside the area.
The GDPR provides a comprehensive framework for protecting personal data and grants individuals greater control over their personal information. However, compliance with the GDPR poses challenges for businesses that deal with European citizens' data.
A common example of GDPR cross-border data transfer is outsourcing services within Europe. Say your branch is in Germany, and your company outsources customer service operations to Bulgaria.
GDPR recommends incorporating data protection measures like pseudonymization, anonymization, encryption, and access controls to enhance the security of your data during transfers to Bulgaria.
However, the regulation does not specify the ideal methods for your specific use case. Each organization must evaluate this independently.
While some methods offer robust protection, they may compromise data quality, while others may not ensure sufficient data security for compliance. The goal is to find a solution that avoids this tradeoff, a topic we will explore further in this guide.
1. GDPR Cross-Border Data Transfer
Cross-border data transfer projects under GDPR cover moving or sharing personal data within the European Economic Area (EEA) and to another jurisdiction outside the area.
The GDPR provides a comprehensive framework for protecting personal data and grants individuals greater control over their personal information. However, compliance with the GDPR poses challenges for businesses that deal with European citizens' data.
A common example of GDPR cross-border data transfer is outsourcing services within Europe. Say your branch is in Germany, and your company outsources customer service operations to Bulgaria.
GDPR recommends incorporating data protection measures like pseudonymization, anonymization, encryption, and access controls to enhance the security of your data during transfers to Bulgaria.
However, the regulation does not specify the ideal methods for your specific use case. Each organization must evaluate this independently.
While some methods offer robust protection, they may compromise data quality, while others may not ensure sufficient data security for compliance. The goal is to find a solution that avoids this tradeoff, a topic we will explore further in this guide.
2. U.S.-EU Cross-border Data Transfers (With Historical Context)
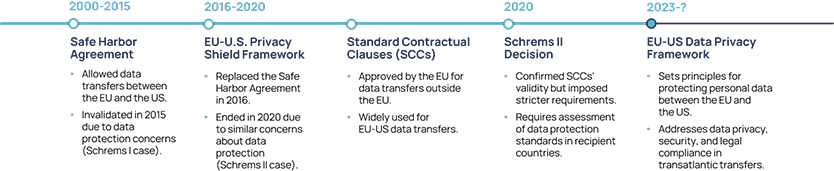
Between 2000 and 2015, the Safe Harbor Agreement served as a key mechanism for data transfers between the EU and the U.S., trying to comply with EU data protection laws. However, the European Court of Justice (ECJ) invalidated it in 2015, citing concerns about inadequate data protection standards in the U.S.
The landmark Schrems I case, initiated by Austrian privacy activist Max Schrems, was pivotal in ending the Safe Harbor Agreement. The ECJ ruled that the agreement failed to adequately protect the privacy rights of EU citizens when their data was transferred to the U.S.
In response to the invalidation of the Safe Harbor Agreement, the EU and the U.S. negotiated the Privacy Shield Framework. The Privacy Shield aimed to provide a legal mechanism for transatlantic data transfers while addressing the shortcomings of its predecessor.
However, the Schrems II case further challenged the validity of the Privacy Shield Framework, highlighting concerns about U.S. government surveillance practices and access to EU citizens' data. The ECJ's ruling invalidated the Privacy Shield in 2020, emphasizing the need for stronger data protection safeguards and legal remedies for EU citizens.
As of July 2023, the EU Commission adopted an adequacy decision for the revamped EU-U.S. Data Privacy Framework, providing a foundation for more secure and compliant data transfers between the two regions.
The increasing number of data sovereignty laws restrict the ability to process and transfer cleartext or encrypted versions of data.
For example, notwithstanding the existence of the EU-U.S. Data Privacy Framework, encryption mechanisms alone can’t solve customers’ challenges described in the EDPB guidance for international data transfers (pages 34 & 35), which still remain relevant for mitigating risks presented by the U.S. CLOUD Act (Clarifying Lawful Overseas Use of Data).
When it comes to the future of EU-U.S. data transfers, K&L Gates writes that:
The landmark Schrems I case, initiated by Austrian privacy activist Max Schrems, was pivotal in ending the Safe Harbor Agreement. The ECJ ruled that the agreement failed to adequately protect the privacy rights of EU citizens when their data was transferred to the U.S.
In response to the invalidation of the Safe Harbor Agreement, the EU and the U.S. negotiated the Privacy Shield Framework. The Privacy Shield aimed to provide a legal mechanism for transatlantic data transfers while addressing the shortcomings of its predecessor.
However, the Schrems II case further challenged the validity of the Privacy Shield Framework, highlighting concerns about U.S. government surveillance practices and access to EU citizens' data. The ECJ's ruling invalidated the Privacy Shield in 2020, emphasizing the need for stronger data protection safeguards and legal remedies for EU citizens.
As of July 2023, the EU Commission adopted an adequacy decision for the revamped EU-U.S. Data Privacy Framework, providing a foundation for more secure and compliant data transfers between the two regions.
The increasing number of data sovereignty laws restrict the ability to process and transfer cleartext or encrypted versions of data.
For example, notwithstanding the existence of the EU-U.S. Data Privacy Framework, encryption mechanisms alone can’t solve customers’ challenges described in the EDPB guidance for international data transfers (pages 34 & 35), which still remain relevant for mitigating risks presented by the U.S. CLOUD Act (Clarifying Lawful Overseas Use of Data).
When it comes to the future of EU-U.S. data transfers, K&L Gates writes that:
“On 10 July 2023 – nearly three years to the day after the Schrems II decision of the Court of Justice for the European Union (CJEU) - the EU Commission adopted the adequacy decision for the new and entirely revamped EU-U.S. Data Privacy Framework (DPF) as a means to secure transfers of personal data from the European Union to companies in the United States.
This decision is a separate tool to justify data transfers under Chapter V of the General Data Protection Regulation (GDPR). It stands next to other established means, such as Standard Contractual Clauses, Binding Corporate Rules, or Codes of Conduct.
The adoption decision will allow data transfers from the European Union (or by companies otherwise subject to the GDPR) to companies in the United States that have signed up to the DPF program and are thus required to meet certain data protection minimum standards.”
This decision is a separate tool to justify data transfers under Chapter V of the General Data Protection Regulation (GDPR). It stands next to other established means, such as Standard Contractual Clauses, Binding Corporate Rules, or Codes of Conduct.
The adoption decision will allow data transfers from the European Union (or by companies otherwise subject to the GDPR) to companies in the United States that have signed up to the DPF program and are thus required to meet certain data protection minimum standards.”
3. India Cross-Border Data Transfer
In August 2023, the Indian Parliament passed the Digital Personal Data Protection (DPDP) Act. This new law marks a significant milestone as it is the initial comprehensive legislation on personal data protection across various sectors in India. The discussions over the scope and shape of the regulation were long, but finally, the law is in full swing.
As you can imagine, the DPDP Act regulates how digital personal data is gathered, processed, stored, and shared. Similarly to the GDPR, the law doesn’t just apply to Indian companies handling personal data. It also covers foreign companies that provide goods or services to people in India and process their data.
So, if your business is planning to run an international data project where India or data of Indian citizens are involved, taking a longer read about all the intricacies will help you decide on the right approach.
An example can be an Indian e-commerce company that transfers customer order data to its cloud servers located in the United States for storage and processing. Compliance with Indian data protection laws requires ensuring that personal data transferred abroad receives adequate protection, aligning with data localization requirements and privacy regulations.
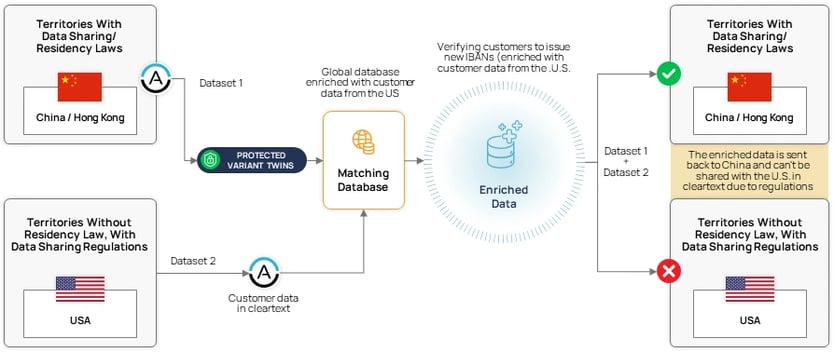
4. China Cross-Border Data Transfer (PIPL)
The Personal Information Protection Law (PIPL) introduced in 2021 marks a big step forward for data privacy in China. Instead of replacing old laws, PIPL adds to them, strengthening data protection.
It focuses on giving people more control over their personal information and ensuring companies handle data responsibly. PIPL sets clear rules for collecting, using, and protecting personal data, reflecting China's commitment to making data transfers more regulated.
When it comes to China's cross-border data transfer, there are a couple of rules for you to keep in mind:
-
You must comply with strict data export rules under PIPL, which require approval to move Chinese citizens' data abroad, leading to bureaucratic hurdles.
-
If you want to pursue a project involving the data of Chinese citizens, you must store specific data within China (e.g., invest in setting up a cloud environment within Chinese territory).
-
You need to get explicit consent for cross-border data transfers.
-
You’ll have to put stricter data protection measures in place, raising your business' responsibilities and risks.
- If you’re a global organization, non-compliance carries hefty penalties, necessitating operational changes. PIPL's impact on global business operations means your global corporation must adapt to stay compliant.
If you’re planning to pursue a cross-border data project within the region, we’d advise you to dive deeper into the intricacies of local jurisdictions. It is also because of the complex political, social, and economic landscape concerning China and Hong Kong.
5. Japan Cross-Border Data Transfer
In Japan, the Act on the Protection of Personal Information (APPI) oversees privacy concerns. At the same time, the Personal Information Protection Commission (PPC) serves as the main supervisory body for privacy protection matters.
Speaking about business, APPI applies to private business operators. Under the APPI, transferring personal data to third parties in foreign countries requires data subjects' prior consent unless the country is white-listed or has equivalent privacy standards (currently, the UK and EU countries are).
According to Japanese law, businesses that want to do cross-border data projects must recognize specific standards, including an acceptable framework like the APEC CBPR system.
Businesses must inform data subjects about the receiving country, its data protection laws, and the measures implemented. Moreover, they must ensure the receiving party continuously adheres to APPI standards. These regulations aim to safeguard personal information during cross-border transfers in compliance with APPI guidelines.
For example, a Japanese multinational corporation may transfer employee data between its headquarters in Tokyo and regional offices in other countries.
To comply with Japanese data protection laws, the corporation should implement measures like:
-
Encryption, access controls, anonymization, and data minimization to safeguard employee data during transfer and storage.
-
Provide employees with clear information about the destination country, its data protection laws, and the measures implemented by the corporation to protect their data.
- Obtain explicit consent from employees before transferring their data to other countries.
-
Obtain certification under the APEC CBPR system, demonstrating adherence to its principles and standards for cross-border data transfers.
-
Demonstrate accountability by establishing internal policies and procedures for handling personal data according to APEC CBPR requirements.
- Maintain transparency by providing clear and accessible information to employees about the corporation's data protection practices and compliance with APEC CBPR standards.
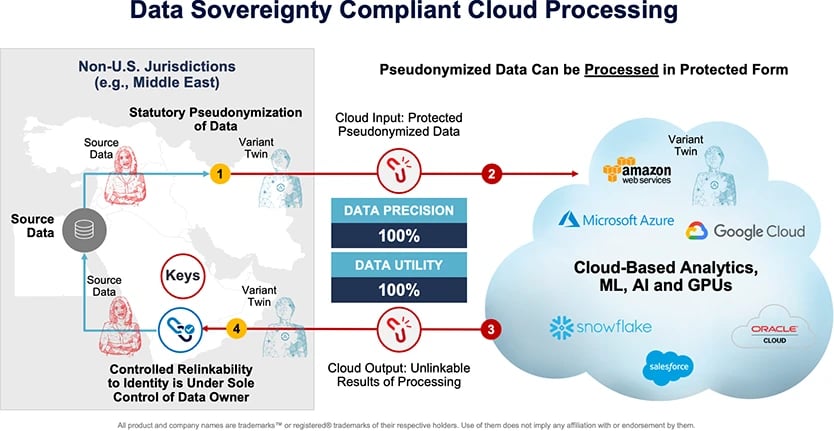
6. Middle East Cross-Border Data Transfer
In the Middle East, despite relatively fewer companies outsourcing operations compared to other regions, it is a significant business center witnessing a rise in data protection regulations.
As of 2024, the Middle East mirrors Europe's GDPR phase 2018, emphasizing crafting precise legislation, mainly concerning personal data. Influenced by royal families, there's a strong commitment to developing and thoughtfully implementing comprehensive data protection laws.
This dedication underscores a growing recognition of the importance of safeguarding user data, particularly evident in countries like Saudi Arabia and the Gulf states.
Speaking about the Kingdom of Saudi Arabia (KSA). They fall under the Personal Data Protection Law ("PDPL") when it comes into effect and Personal Data Protection Interim Regulations ("PDPIR") issued by the National Data Management Office ("NDMO").
Their PDPIR law states that Data Controllers must get written approval from the appropriate Regulatory Authority before storing and handling Personal Data outside KSA.
The United Arab Emirates (UAE) has enacted the UAE Personal Data Protection Law (PDPL), which is even stricter than PDPIR and mandates organizations to secure consent before transferring personal data beyond national borders.
The key distinction between PDPL and GDPR is that PDPL extends its scope to include the data of deceased individuals and their families. This broader scope sets PDPL apart because, once someone passes away in Europe, they're no longer considered a data subject under GDPR.
The Middle East's proactive approach to enforcing data protection regulations reflects a broader trend toward prioritizing user privacy and data security across the region.
And no doubt why it happens. Gulf countries are building AI and smart cities, and there are many opportunities to realize cross-border data projects. Data protection rules are supposed to ensure data is used ethically for improving cities and public services. They also build trust, attract investment, and reduce cyber risks in the digital economy.
How Your Business Should Navigate Cross-Border Data Transfer Challenges
Navigating cross-border data transfers can be a bit tricky, but fear not! Your business can thrive in these endeavors by keeping a few key criteria in mind:
-
Data Protection: Ensuring data remains secure during transfer is key for your business. The stakes are high – fines under the GDPR can reach up to €20 million or 4% of the company's annual global turnover, whichever is higher.
-
Data usability: Data must maintain its quality and integrity post-transfer so data teams can use data as a competitive advantage. For example, a global institution’s data team needs high-quality data to deploy AI-driven chatbots that enhance customer experience.
- Time to data: Quick access to data is essential for operational efficiency and success of an analytics project. When it takes too long to access data, you may lose opportunities to capitalize on emerging trends. Project deadlines may be extended, leading to increased costs and resources.
Many traditional data protection methods, like basic masking or tokenization, may compromise data quality and usability and not provide adequate protection. At the same time, if your business does manual privacy assessments, it can be time-consuming, impeding prompt data access to ensure compliance.
Another issue is agreements such as SCC and BCR. They help establish and support lawful data transfers between jurisdictions, but words alone don’t technologically ensure compliance and eliminate the possibility of a breach.
Another issue is agreements such as SCC and BCR. They help establish and support lawful data transfers between jurisdictions, but words alone don’t technologically ensure compliance and eliminate the possibility of a breach.
Therefore, selecting the right protection solution is paramount. And fortunately, solutions to make your cross-border transfer smooth exist. Take a look at the specific tactics.
Zero-trust data derives from the Zero-Trust Security concept, which has the same fundamental principle of minimizing trust assumptions in the digital realm. If you’re new to zero-trust topics, let’s briefly address the difference between Zero-Trust Security and Data.
Zero Trust Security is all about setting up a security system that gives the least privilege and enforcing strict access controls for network resources. Take a look at the chart below.
1. Apply Zero Trust Data™: An Overarching Approach to Your Data Operations
Zero-trust data derives from the Zero-Trust Security concept, which has the same fundamental principle of minimizing trust assumptions in the digital realm. If you’re new to zero-trust topics, let’s briefly address the difference between Zero-Trust Security and Data.
Zero Trust Security is all about setting up a security system that gives the least privilege and enforcing strict access controls for network resources. Take a look at the chart below.
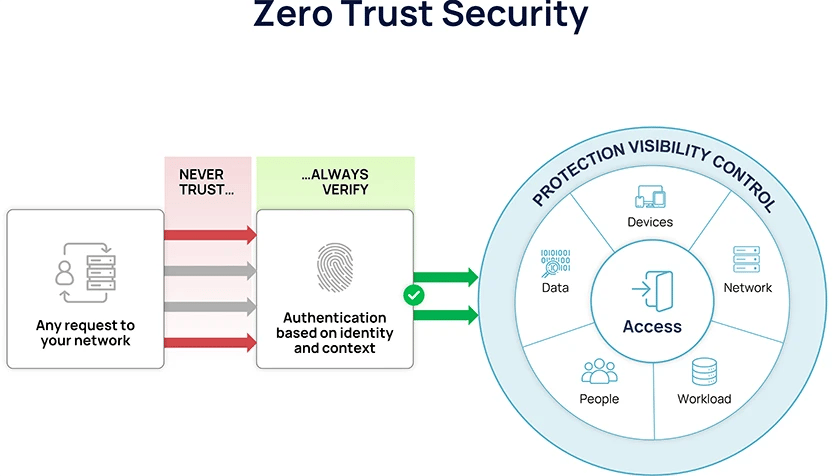
An illustration of the Zero Trust security, Privacy Affairs, 2023
Zero Trust Data focuses on data protection through its entire lifecycle rather than relying on network or perimeter defenses alone. So it applies not only to data at rest or in transit but also to data in use. It highlights the importance of using data-focused security methods to keep information always safe and reduce the chances of data breaches.
In cross-border projects involving AI, ML, and analytics, your branch will deal with sensitive and personal data subject to different data protection laws and regulations across jurisdictions.
Adopting a zero-trust data approach helps organizations maintain and also significantly simplify compliance with these diverse regulatory requirements while ensuring the security and integrity of data throughout its lifecycle. No matter who gets access to data, it stays protected.
Let’s give an example. Say you represent an American global bank branch that wants to share customer transaction data with a Japanese counterpart for a cross-border data project.
Implementing a zero-trust data approach means you’ll protect data access throughout the whole lifecycle, and wherever it lands and whatever state of data is, it’s safe. This is especially important in the state of data being used because, in this state, data is most vulnerable to breaches or misuse.
In the context of AI and ML, where models are trained on large datasets, the zero-trust data approach will ensure that the data used for training and inference purposes remains secure and confidential, even when accessed by third-party vendors or collaborators across borders.
As you work in a security team, you know how important it is to have a strategy for cross-border data transfer.
This strategy should include:
In cross-border projects involving AI, ML, and analytics, your branch will deal with sensitive and personal data subject to different data protection laws and regulations across jurisdictions.
Adopting a zero-trust data approach helps organizations maintain and also significantly simplify compliance with these diverse regulatory requirements while ensuring the security and integrity of data throughout its lifecycle. No matter who gets access to data, it stays protected.
Let’s give an example. Say you represent an American global bank branch that wants to share customer transaction data with a Japanese counterpart for a cross-border data project.
Implementing a zero-trust data approach means you’ll protect data access throughout the whole lifecycle, and wherever it lands and whatever state of data is, it’s safe. This is especially important in the state of data being used because, in this state, data is most vulnerable to breaches or misuse.
In the context of AI and ML, where models are trained on large datasets, the zero-trust data approach will ensure that the data used for training and inference purposes remains secure and confidential, even when accessed by third-party vendors or collaborators across borders.
2. Understand the Data Residency Laws, Your Use Cases, and Align Privacy & Security Teams
As you work in a security team, you know how important it is to have a strategy for cross-border data transfer.
This strategy should include:
-
Understanding and complying with data protection regulations applicable to both the originating and destination countries or regions.
-
Analyzing your use cases for cross-border data transfer to set up the purpose of transferring data across borders.
-
Classifying data based on sensitivity and regulatory requirements. Different types of data may have different regulatory constraints and security requirements.
-
Guidelines to implement robust security measures to protect data during transit and at rest.
-
Establishing collaboration and alignment between your team and privacy and data teams to ensure that data transfer activities meet both privacy and security requirements while still holding analytical value.
-
Setting up guidelines for training teams on data protection protocols and compliance requirements so your organizations can effectively manage risks and govern data effectively.