Top Six Takeaways from the Webinar
01
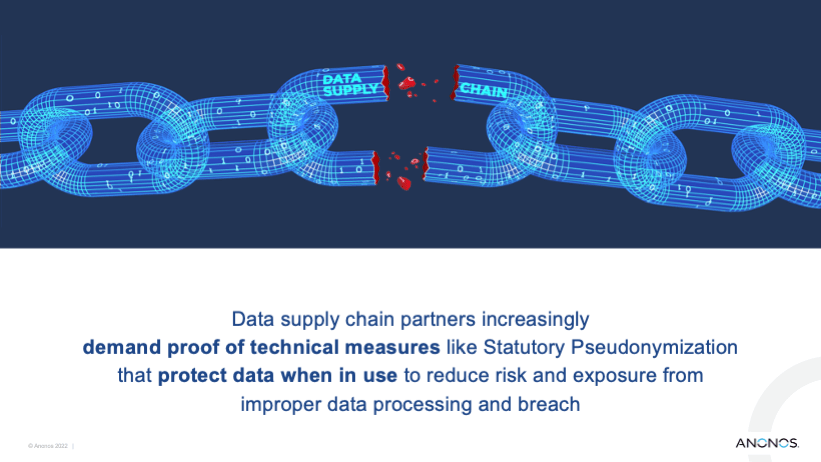
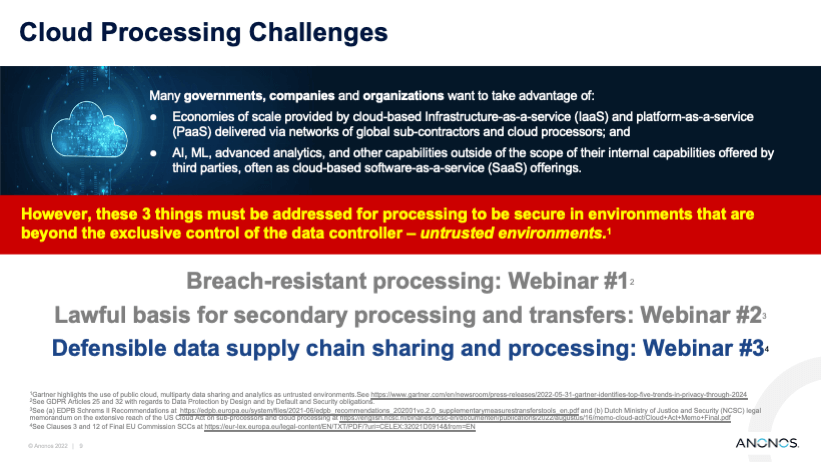
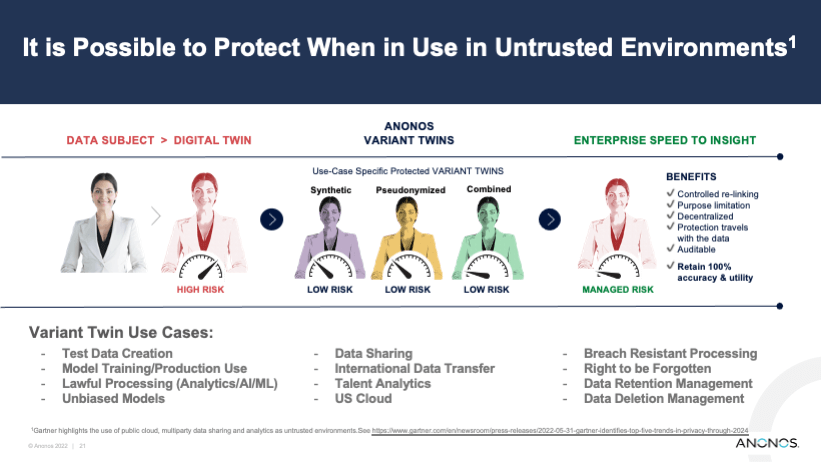
The use of the U.S. cloud as part of organizational data supply chains is critical, and needs to continue for both operational and business reasons.
02
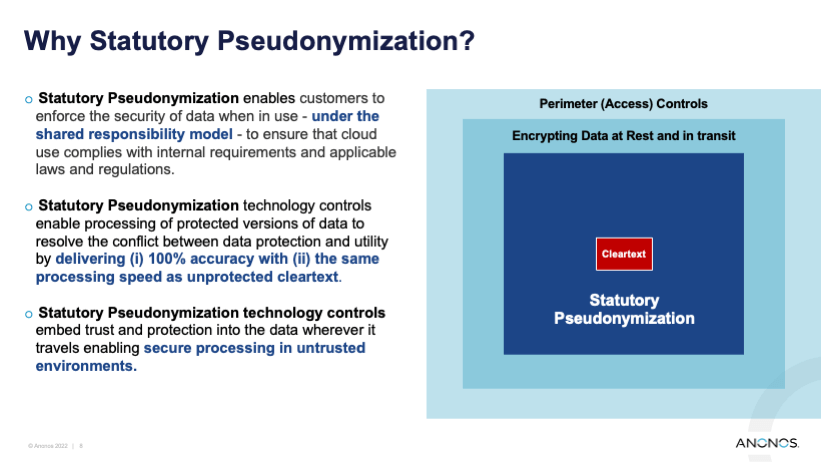
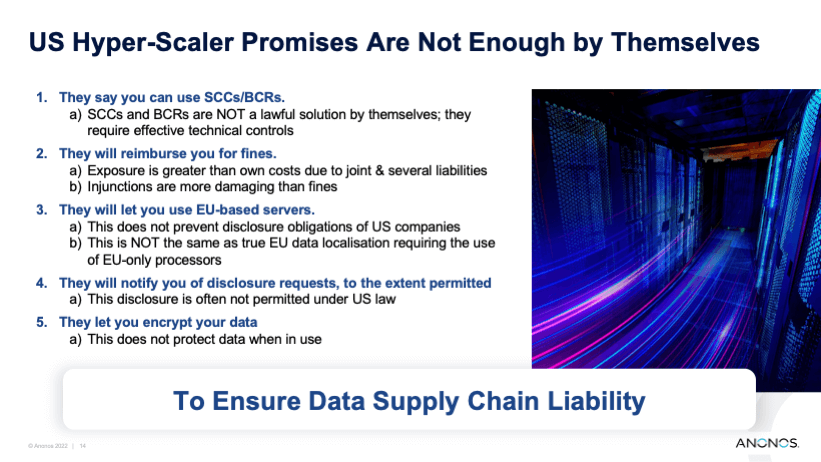
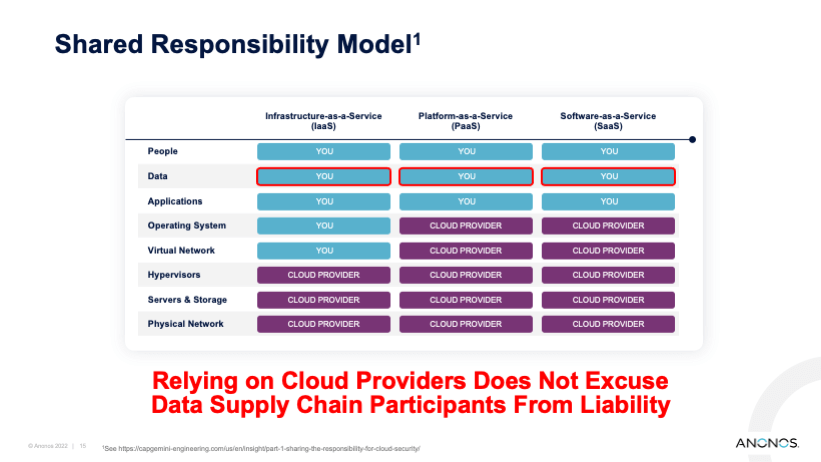
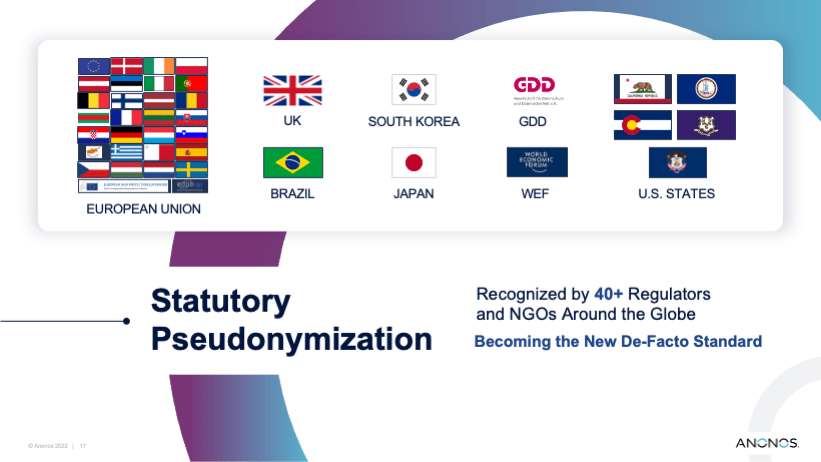
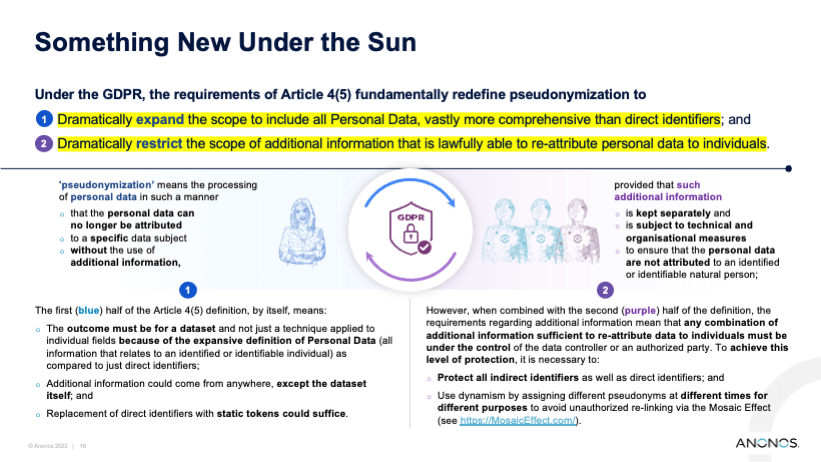
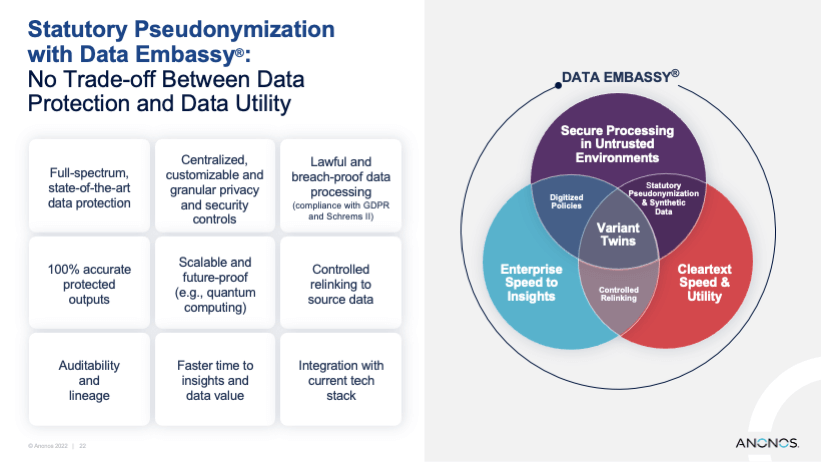
Joint and several liability and the shared responsibility model apply to the use of the cloud, for cloud providers and cloud users. Increasing technical protections such as through the use of Statutory Pseudonymization can reduce the risk of breach and help organizations more easily obtain cybersecurity insurance.
03
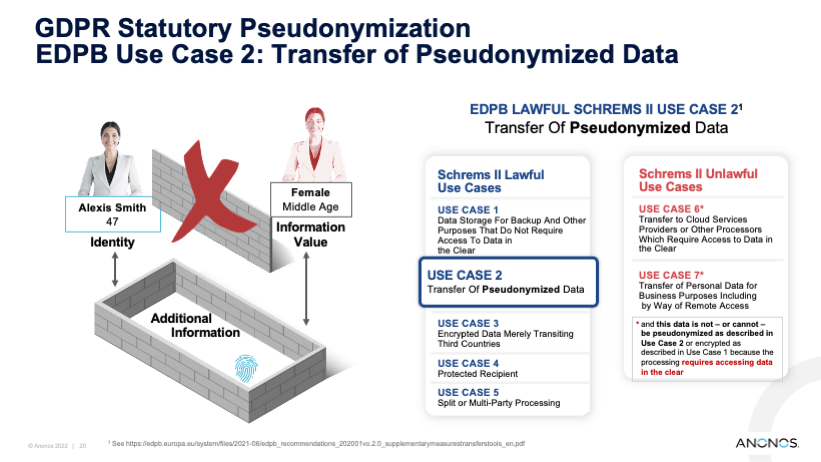
Schrems II and other guidance does not intend to prohibit the use of the U.S cloud; instead, compliant use is the intention by leveraging technical controls.
04
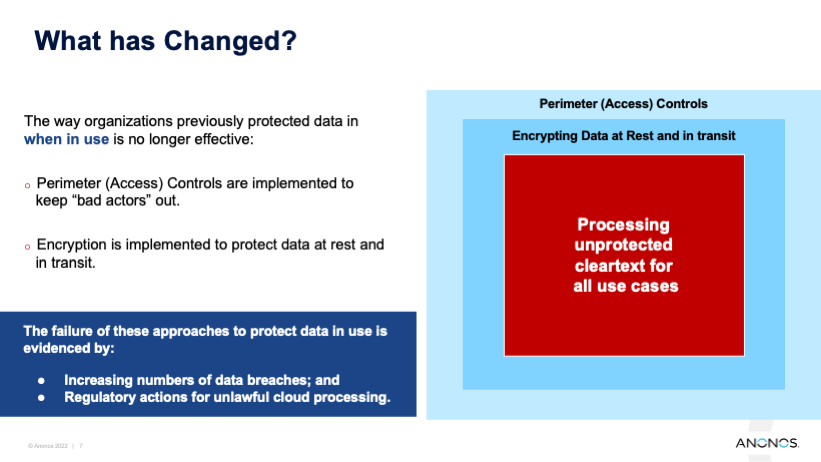
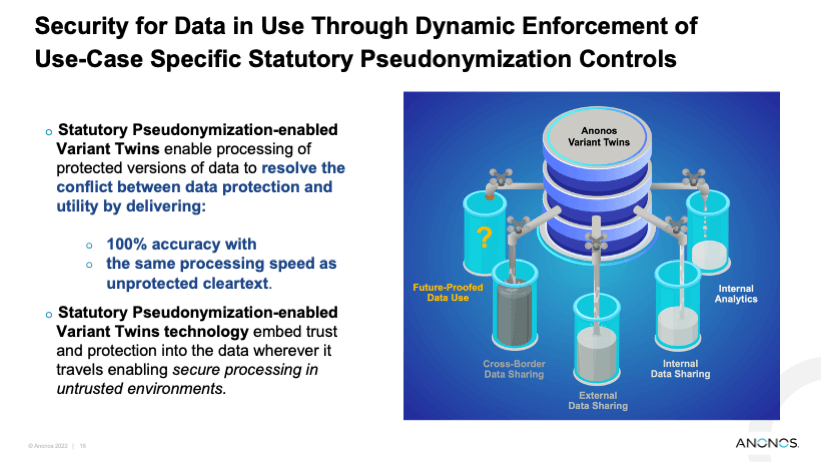
Access controls and encryption only protect data in transit and in storage, but most data is still processed in cleartext, leaving it vulnerable to breach.
05
The U.S. cloud can be used in a compliant manner with appropriate technical and organizational controls.
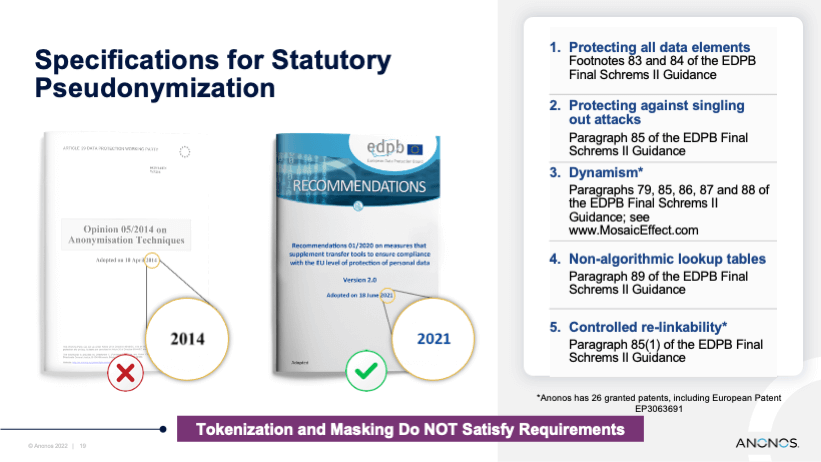
06
Statutory Pseudonymization allows EU-US transfers and compliant processing, including compliant further processing in the cloud for AI, ML and analytics.