Top Six Takeaways from the Webinar
01
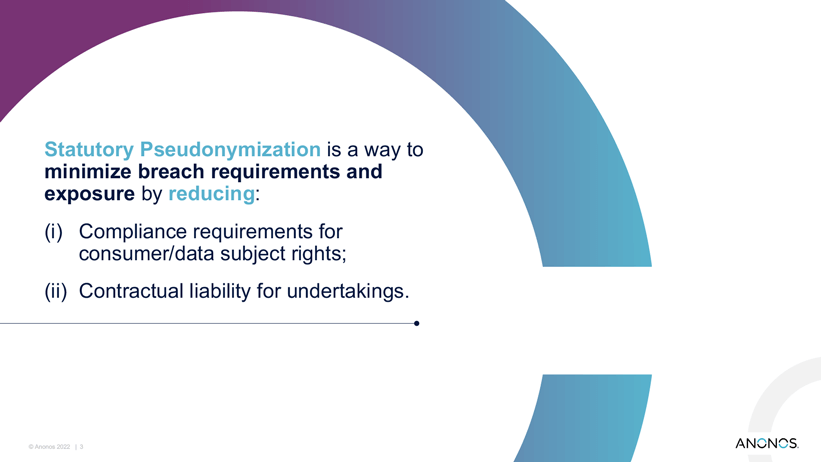
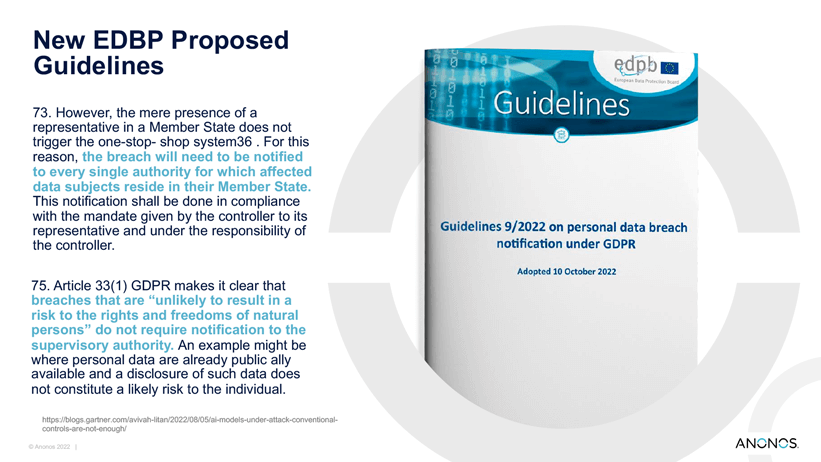
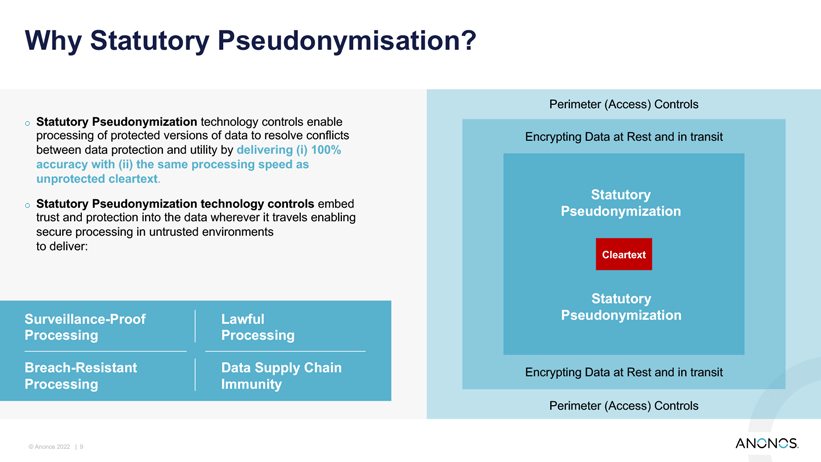
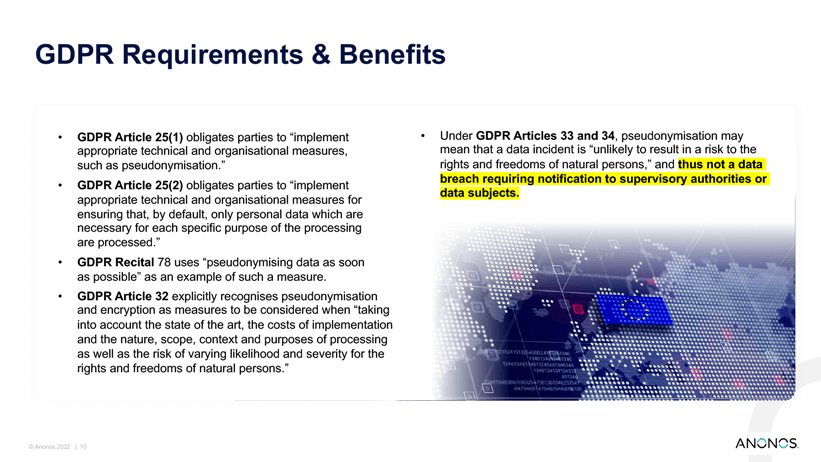
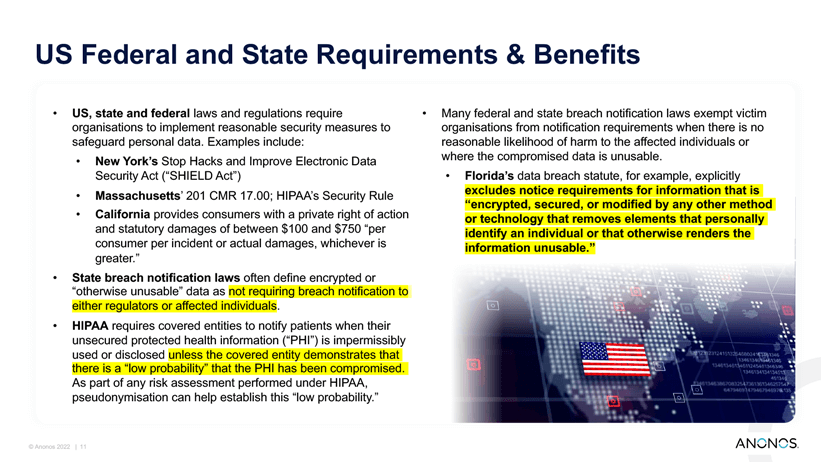
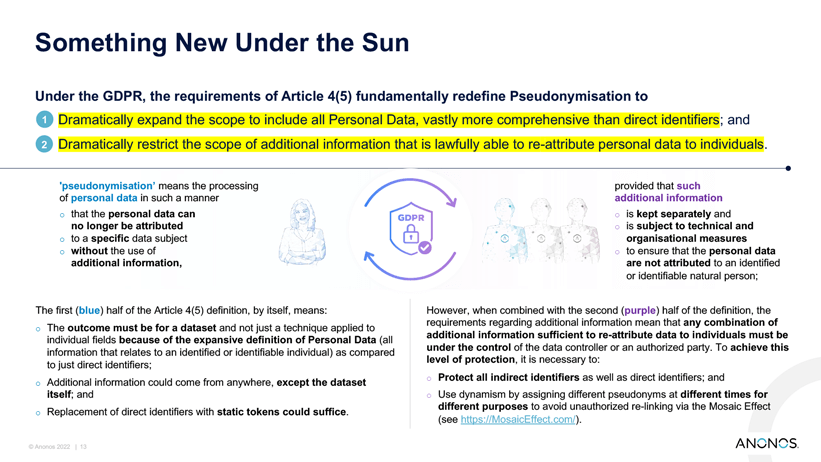
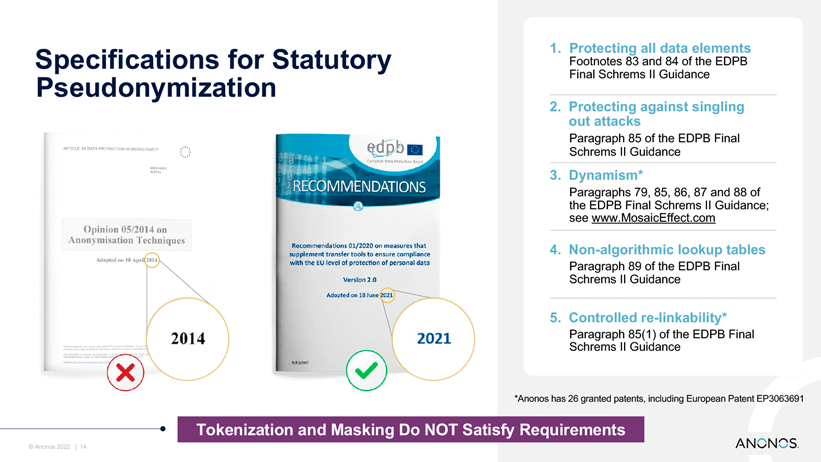
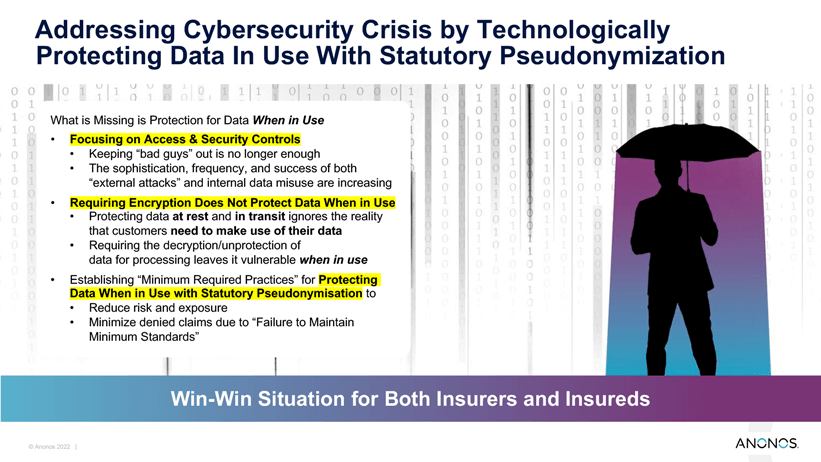
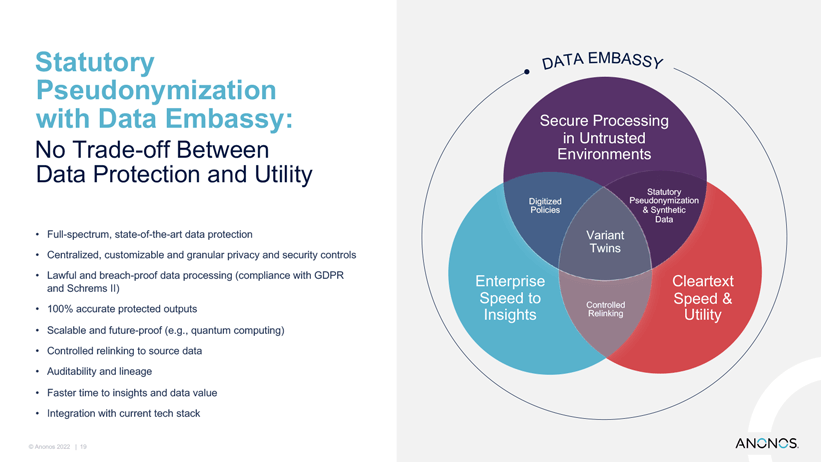
Reduces organizations’ obligations under the GDPR, as far as notification of data subjects and regulators. By protecting data in line with GDPR recommendations, organizations reduce their breach exposure in the first instance, as well as compliance obligations
02
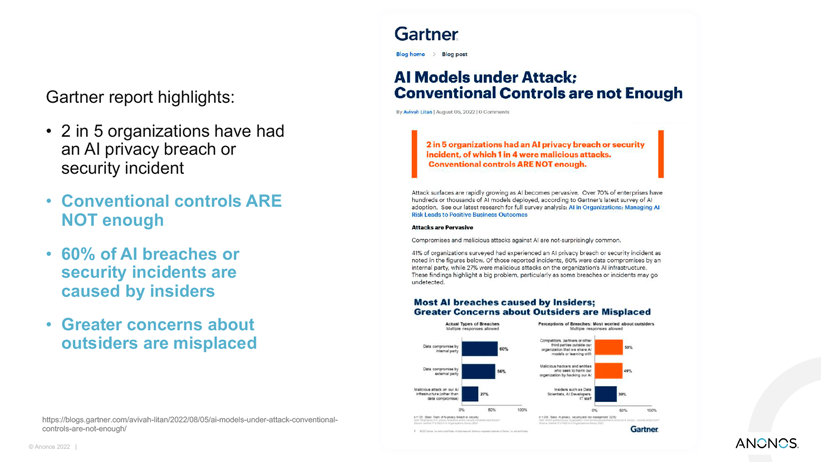
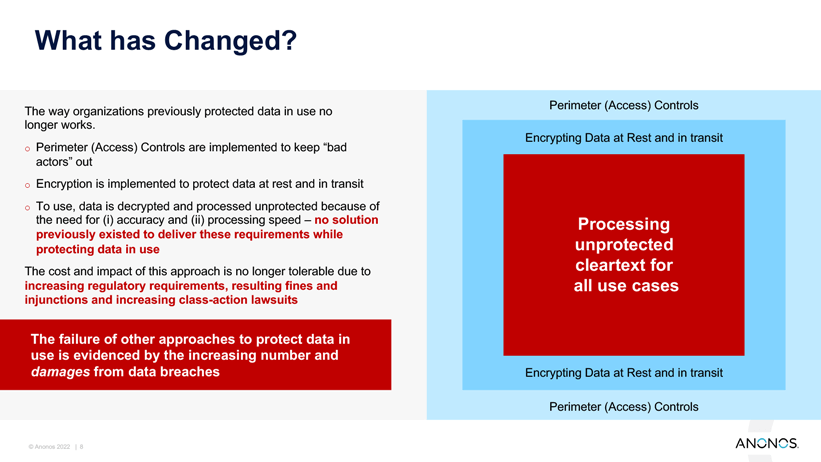
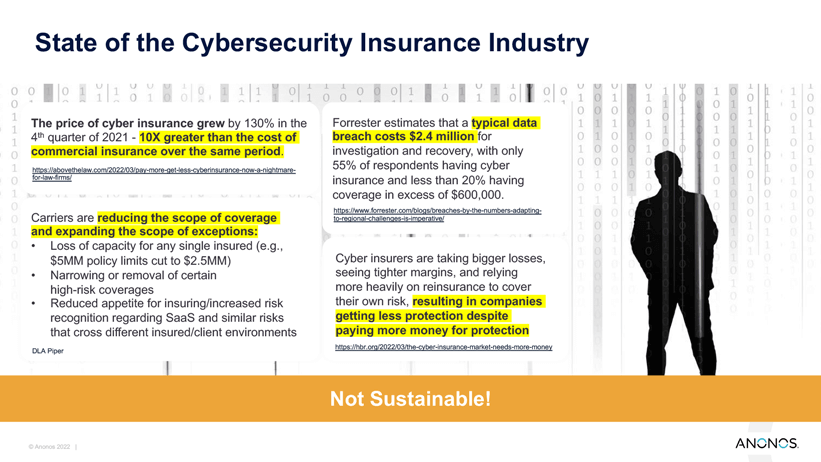
Protects data, rendering it useless to any attacker in the event that a breach occurs. Measures such as statutory pseudonymization can play a crucial role in protecting organizations from the consequences of a breach once one has occurred.
03
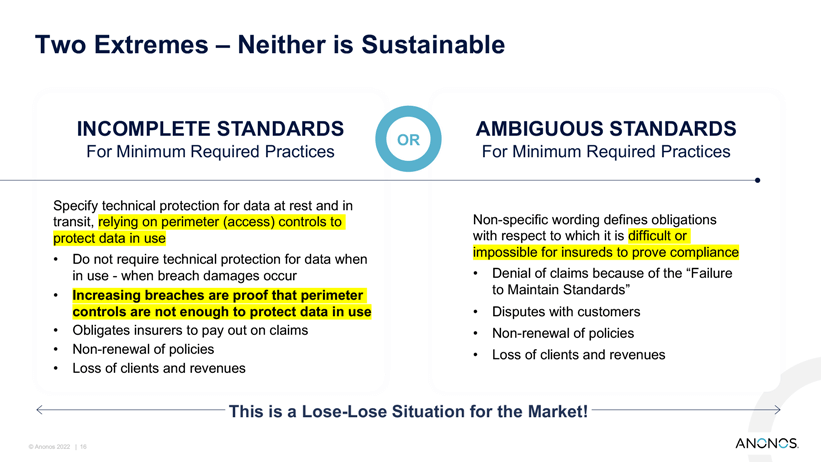
Allows organizations to obtain more comprehensive cybersecurity insurance. Organizations should show that they are using approaches such as pseudonymization to protect the data and protect the privacy of data subjects.
04
Data minimization and purpose limitation. When it comes to data collection, organizations should not keep more than what they need.
05
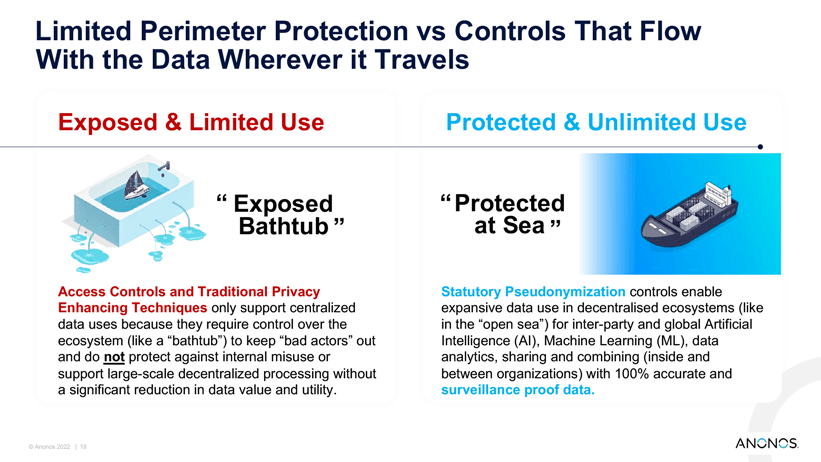
Secondary uses of data. Pseudonymization is one way to enable compatible secondary uses of the data.
06
Protects data both internally and externally. Statutory pseudonymization protects against data breach in both of these cases, by protecting data for both authorized persons and authorized uses, no matter where the data is.