Top Six Takeaways from the Webinar
01
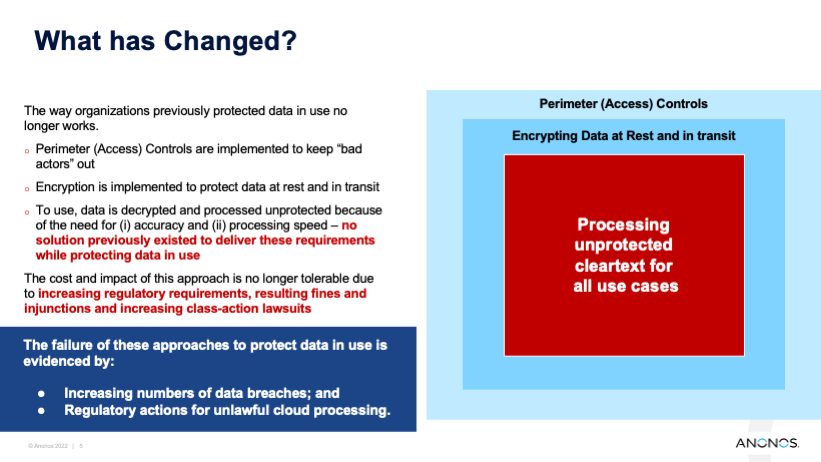
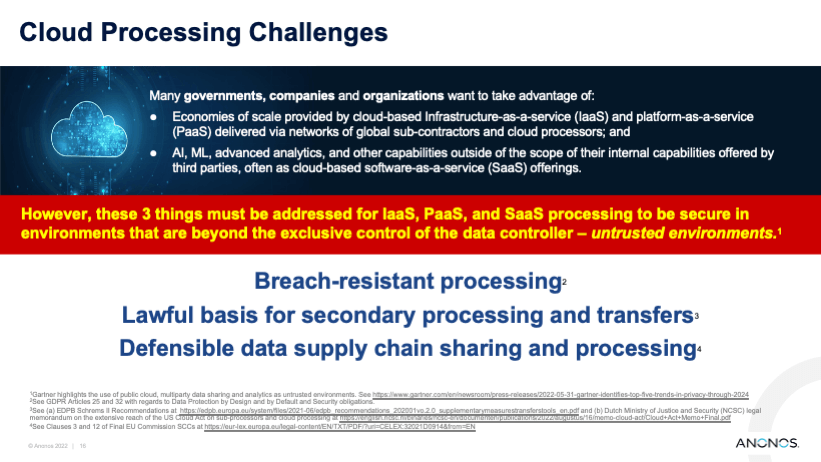
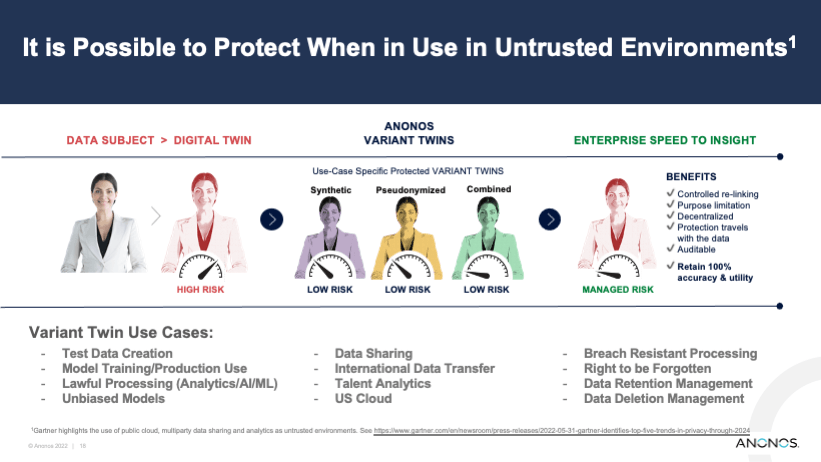
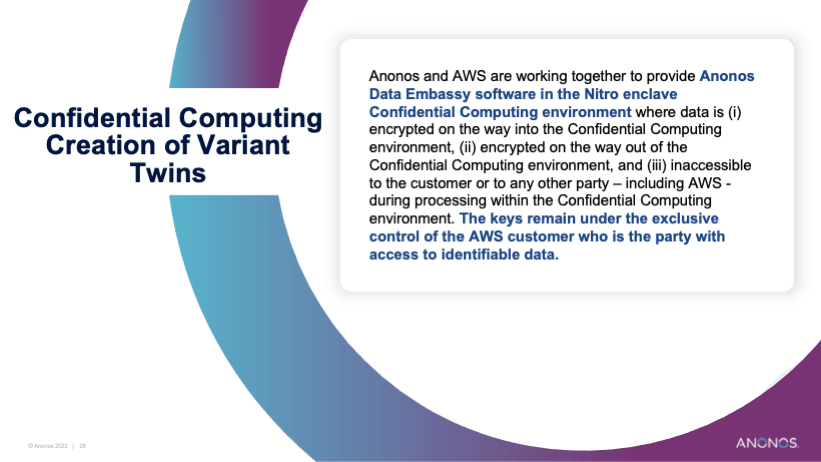
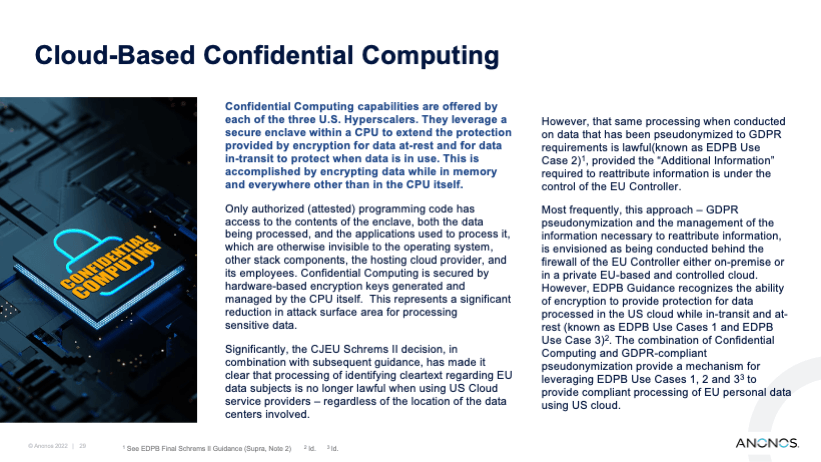
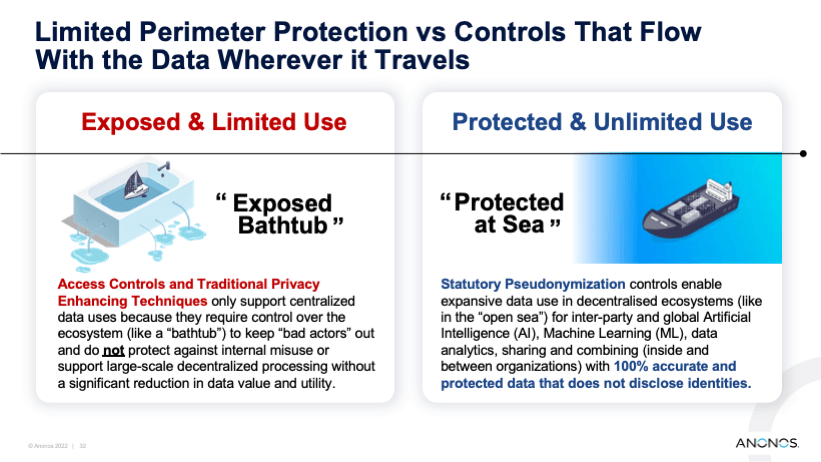
Organizations protect data at rest and in transit with encryption and access controls, but often no controls are used to protect data when it is being processed in cleartext. Numerous data breaches and enforcement actions highlight this issue.
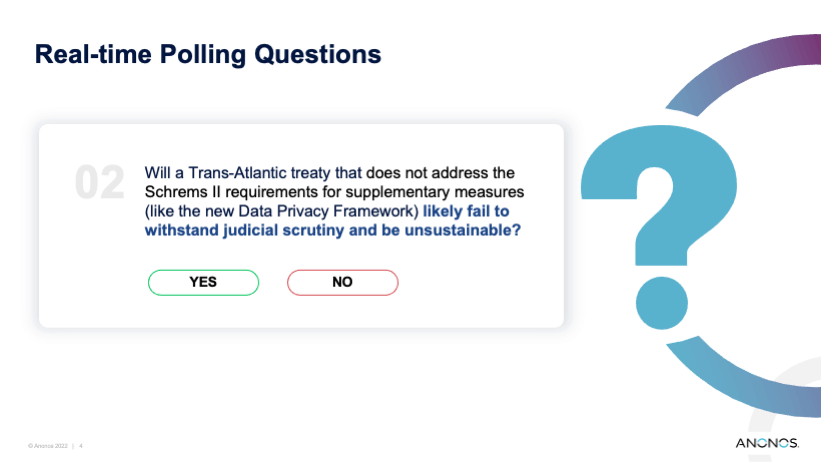
02
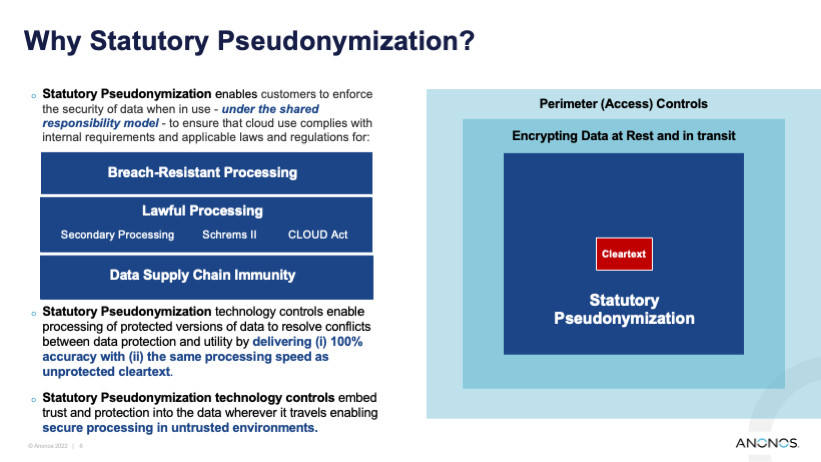
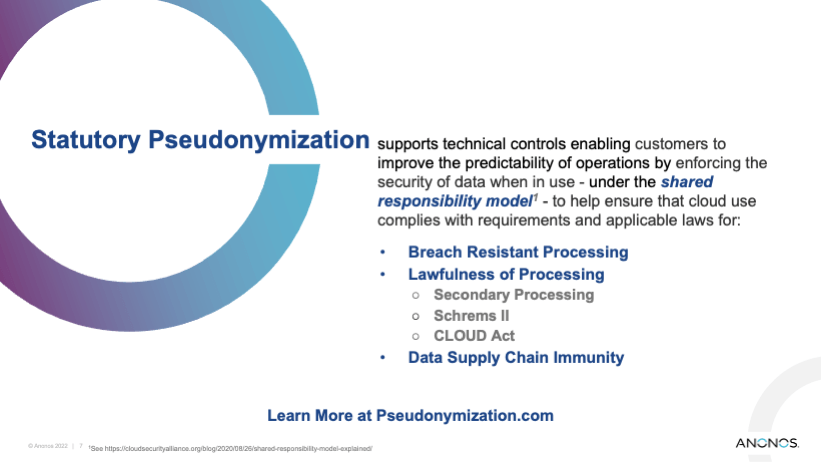
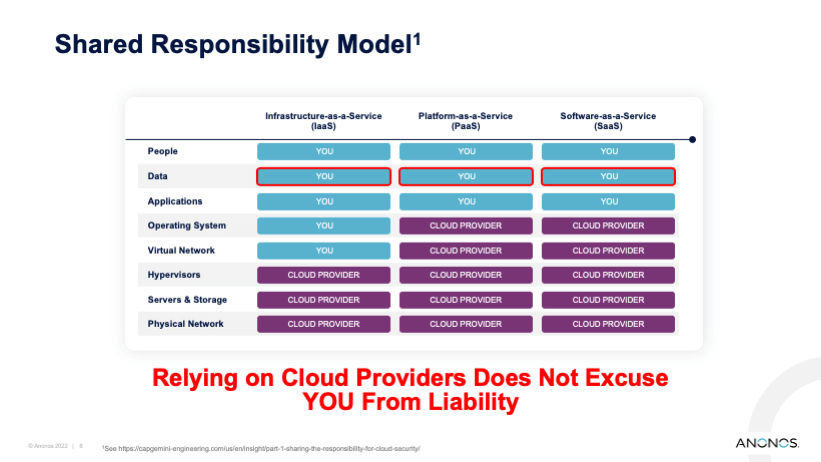
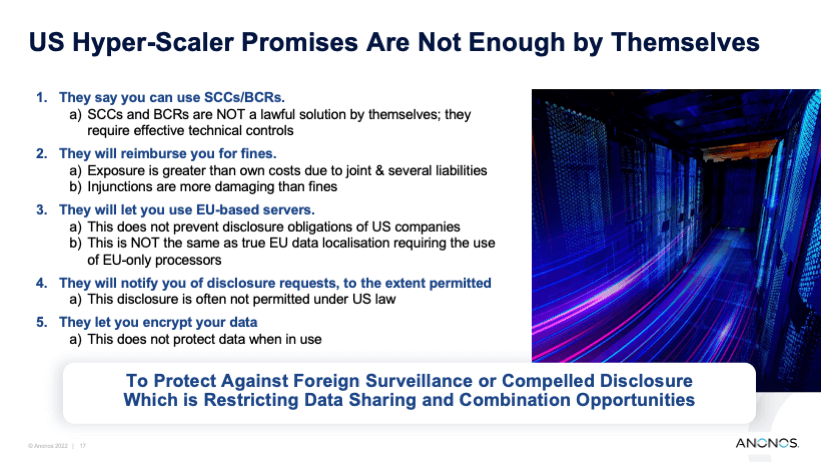
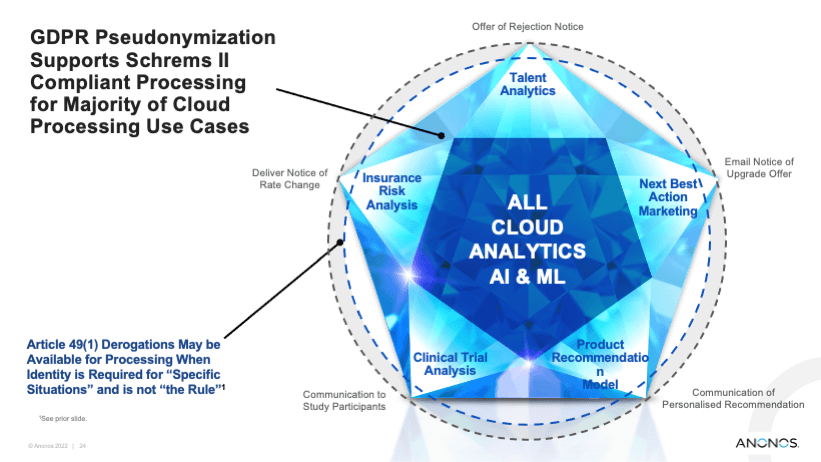
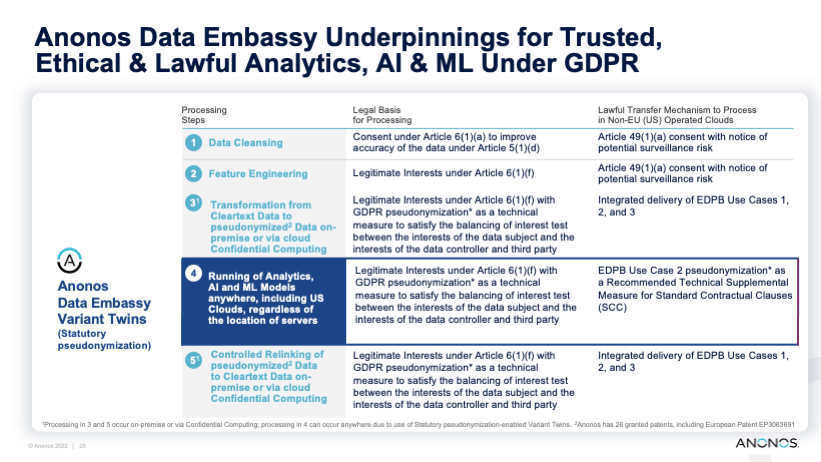
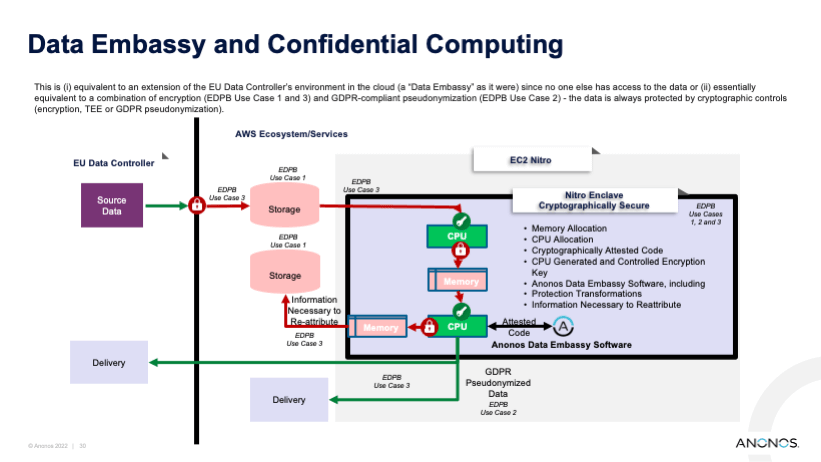
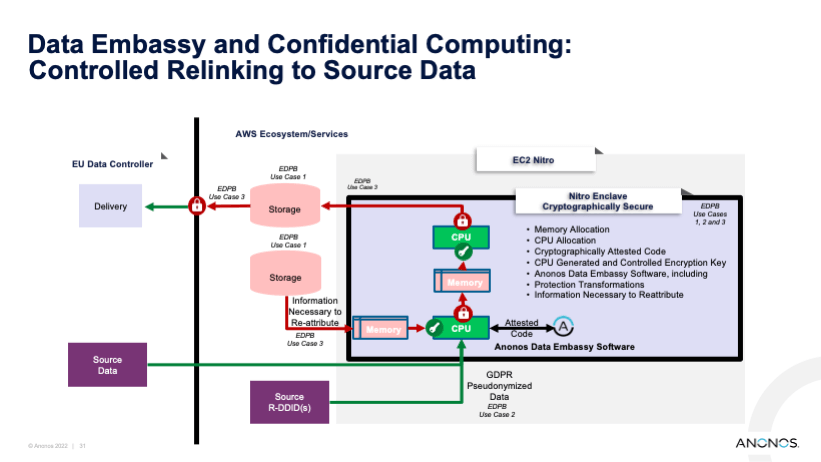
Technical controls that protect data in use are important for protecting against breaches and making desired processing in U.S.-operated clouds lawful.
03
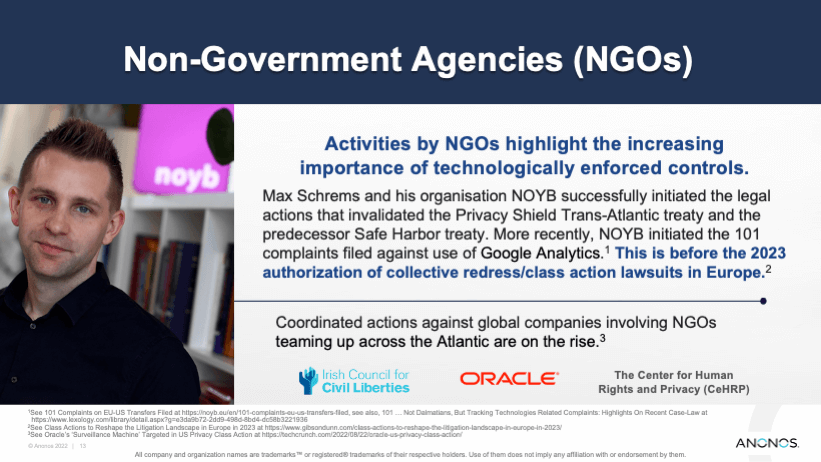
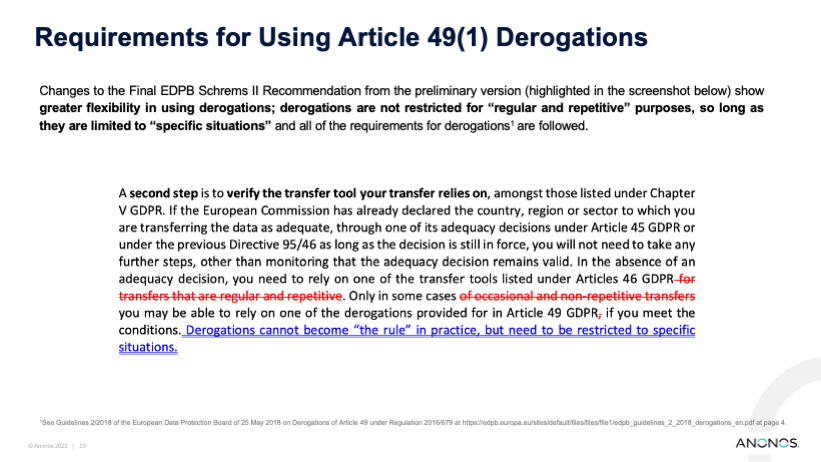
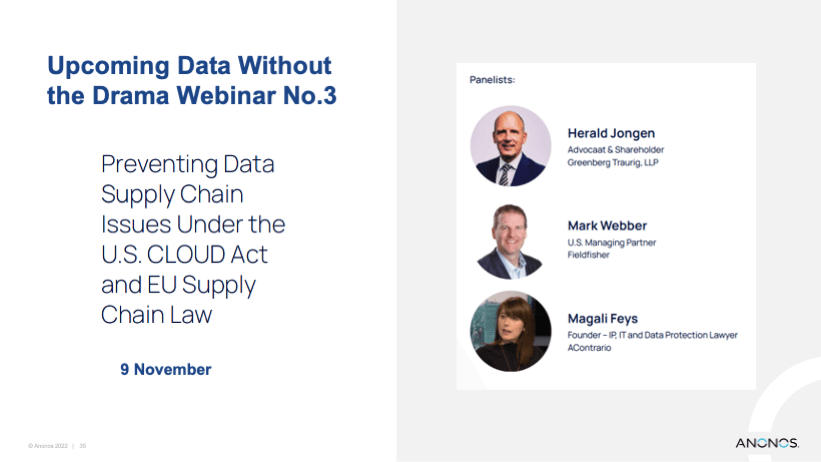
EU and U.S. laws are often in conflict. Technical controls can helpbridge conflict-of-laws issues.
04
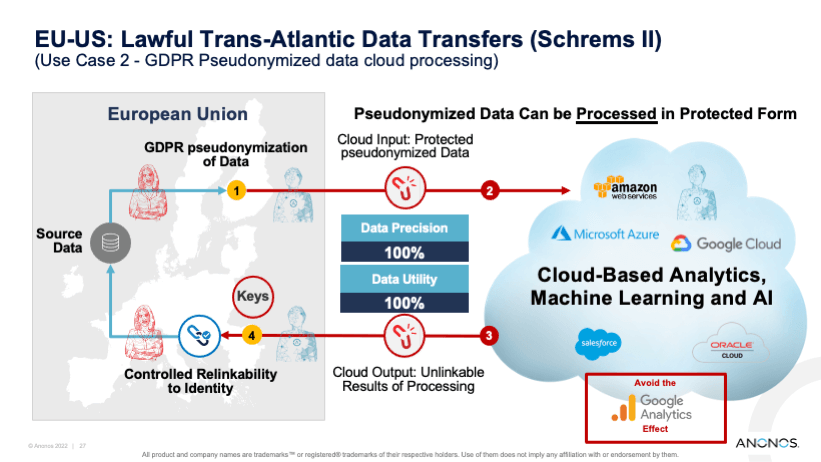
The Schrems II ruling has sparked new interest in the CLOUD Act, and the interplay between U.S. cloud providers, U.S. companies, and EU data subject rights.
05
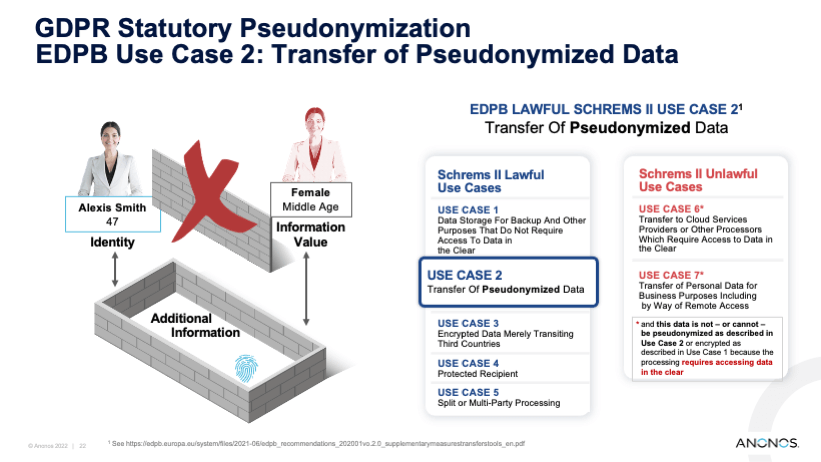
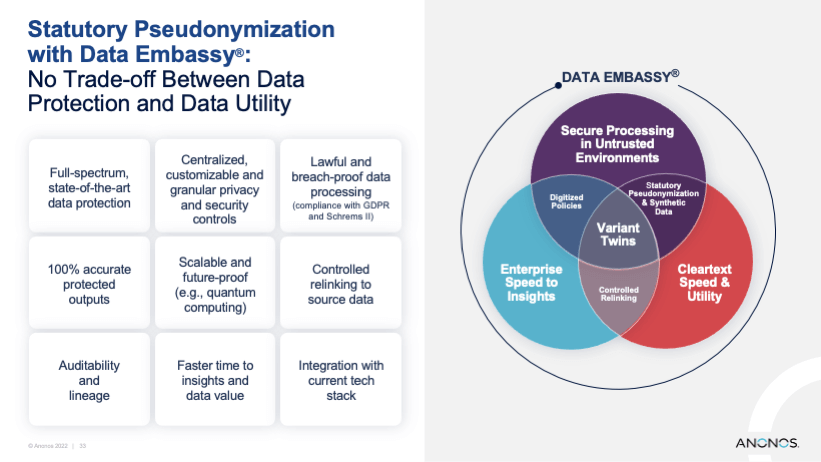
Technical measures can protect against CLOUD Act requests and help reconcile Schrems II issues with EU data subject data.
06
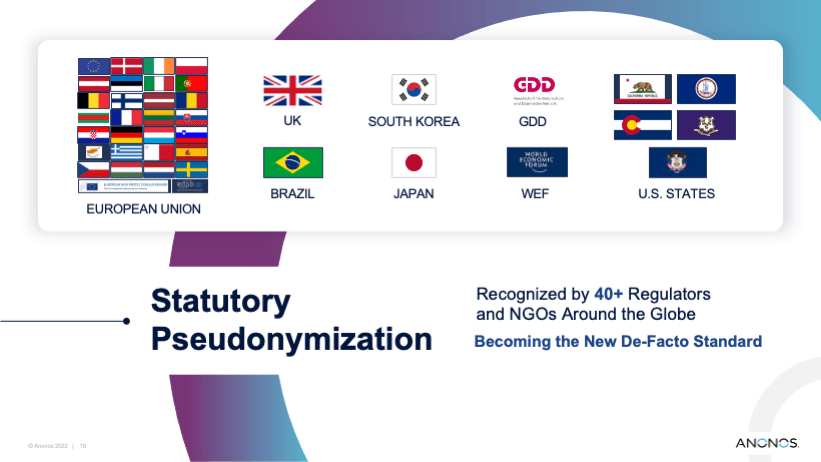
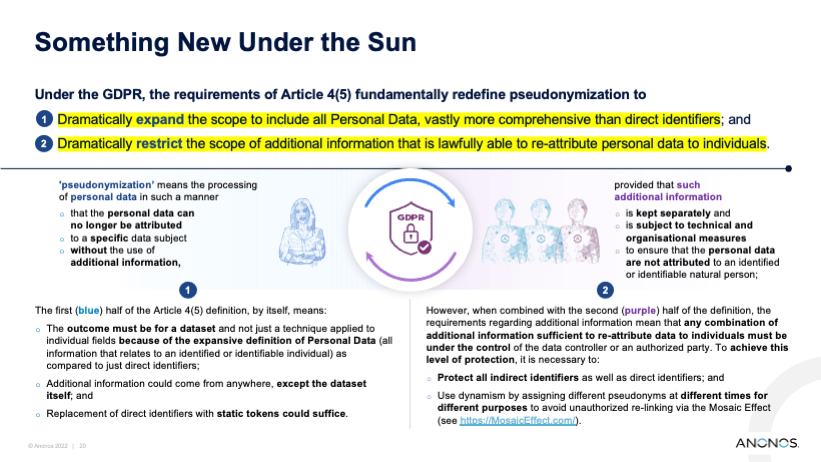
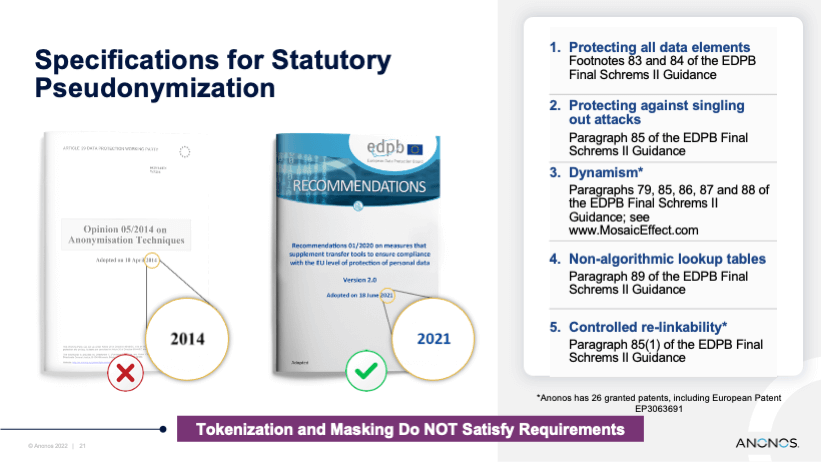
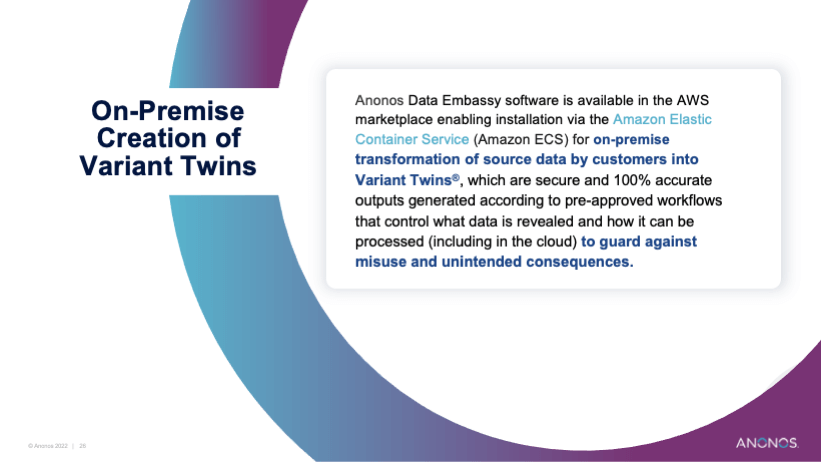
Statutory pseudonymization is one way to enable organizations, governments and companies to process data in a way that is predictable and lawful to enable data-driven insights.