
I start and end this article with the same question - Does GDPR-defined Pseudonymisation Overcome the Shortcomings of Anonymisation and Encryption in Response to the Schrems II / Privacy Shield Decision?
I do this to emphasise the importance of consulting with your advisors about the possible benefits of using Pseudonymisation as newly defined under the GDPR to overcome the inability of anonymisation and encryption to satisfy requirements for “supplemental measures” under Schrems II.[1] Why? So, your organisation can continue to use Standard Contractual Clauses (SCCs) and Binding Corporate Resolutions (BCRs) for lawful international data transfer and processing.
------------
Pending official guidance from the EDPB on Schrems II supplemental measures, data controllers and processors should seek advice from their advisors regarding the potential benefits of GDPR-compliant Pseudonymisation.
------------
If you believe you know the meaning of “Pseudonymisation” under the GDPR but think it is merely a technique, with all due respect you are mistaken. As highlighted in a 29 July 2020 Memorandum to the EDPB; Supplemental Measures Under Schrems II (the “EDPB Memorandum”[2]):
"Pre-GDPR approaches (using a static token on a direct identifier, which unfortunately is still widely and incorrectly referred to as “pseudonymisation”) will rarely, if ever, meet the heightened GDPR requirements of Pseudonymisation. This also means that old approaches known as “pseudonymisation” will not be sufficient to meet the requirements for supplementary measures to enable lawful international data transfers under EU law."
As a lawyer, data protection specialist and Chief Strategist of Ethical Data Use at Anonos, I believe It is helpful to understand the position taken by Max Schrems’ privacy advocacy organization, NOYB, on these matters, since the NOYB is the principal protagonist behind:
The NOYB website and FAQs[4] take the position that US-owned “electronic communication service providers” (NOYB specifically identifies AT&T, Amazon (AWS), Apple, Cloudflare, Dropbox, Facebook, Google, Microsoft, Verizon Media (former Oath & Yahoo), and Verizon) can no longer be used to process EU personal data. NOYB claims this is due to Section 702 of the US Foreign Intelligence Surveillance Act (FISA 702) and US Executive Order 12333 (EO 12333), which specifically require “electronic communication service providers” to comply with US surveillance requests regardless of where data processing occurs - in the US, the EU, or anywhere.
The Schrems II ruling holds that surveillance of EU personal data constitutes a violation of EU fundamental rights. In the opinion of the NOYB, processing of EU personal data by US “electronic communication service providers” fails to comply with GDPR Article 32 Security of Processing requirements even when the data is anonymized[5] or encrypted.[6] Since EU personal data is subject to potential surveillance even if anonymized or encrypted, NOYB states that:
"The data exporter and data importer therefore has to implement appropriate technical and organisational measures to protect transferred data from NSA/FBI tapping...Given that the US government has vast powers to break encryption, it is mainly a technical question in each transfer situation if and how a technical solution is possible."
Organisations desiring to avoid injunctions against further processing, penalties and lawsuits, should be prepared to answer the following question which the NOYB says should be asked of all US controllers and processors if relying on SCCs[7]:
"(5) As the Court of Justice has also highlighted the need to ensure that personal data is not subject to mass surveillance in transit, we seek the following clarifications:
(A) Have you implemented appropriate technical and organisational measures (see Article 32 GDPR) for every step of the processing operations which ensure that mass and indiscriminate processing of personal data by or on behalf of authorities in transit (such as under the “Upstream” program in the US) is made impossible?
(B) If so, please specify which technical and organisational measures (including encryption) have been taken so that neither content nor meta data can be processed by sophisticated state actors with direct access to the internet backbone, switches, hubs, cables and alike."
As highlighted in the EDPB Memorandum:[8]
"The COVID pandemic is accelerating the need for data-driven innovation and digital transformation. However, the Schrems II case ruling by the Court of Justice of the European Union (“CJEU”) has turned the world of international data transfers upside-down. Overnight, thousands of organisations are now looking to the EDPB for timely guidance."
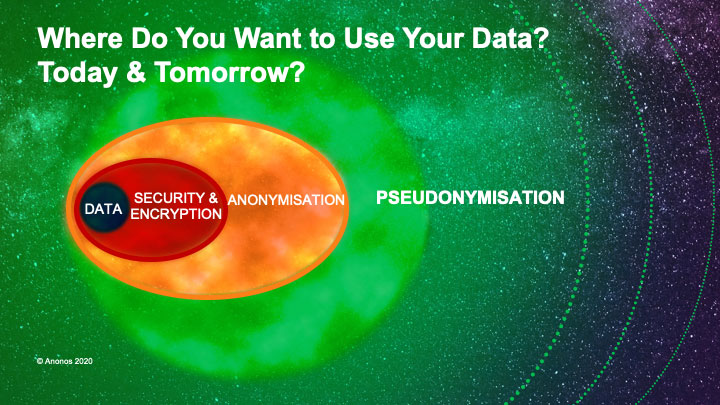
Pending official guidance from the EDPB on Schrems II supplemental measures, data controllers and processors should seek advice from their advisors regarding the potential benefits of GDPR-compliant Pseudonymisation. Pseudonymisation is highlighted in Article 32 as a potential “appropriate technical and organisational [measure] to ensure a level of security appropriate to the risk” to enable lawful secondary processing like analytics, Big Data, AI, ML and BI using non-EU/EEA owned cloud, SaaS and infrastructure providers.
While the GDPR is expressly technology neutral and does not recommend specific techniques,[9] a review of resources published after the effective date of the GDPR,[10] reveals that Pseudonymisation is no longer merely replacing direct identifiers (only) with pseudonymous tokens as it was prior to the GDPR.[11] To satisfy new GDPR definitional requirements under Article 4(5), Pseudonymised data - inclusive of both direct and indirect identifiers, and potentially attributes as well - must now make it impossible to attribute data “to a specific data subject without the use of additional information, provided that such additional information is kept separately and is subject to technical and organisational measures to ensure that the personal data are not attributed to an identified or identifiable natural person.” It is critical to realize that this means Pseudonymisation is now an outcome describing a data set as a whole, it is no longer a technique applied to individual fields in a data set.
As newly defined under the GDPR and as discussed in the EDPB Memorandum,[12] Pseudonymisation does not represent a “silver bullet,” “golden shield,” or “magic wand” that makes your Schrems II / Privacy Shield challenges go away. But it is definitely worth asking your advisors the question:
Does GDPR-defined Pseudonymisation Overcome the Shortcomings of Anonymisation and Encryption in Response to the Schrems II / Privacy Shield Decision?
When consulting with some industry experts, here is what they're saying:
"Global data protection laws evolve and change constantly, but their ultimate goal should be a high level of protection of the rights of the person whose data are collected and used, as well as ensuring that when personal data flows across borders, they continue to be protected. While the fundamental principles of data protection remained constant since the first data protection laws have been adopted, new measures and mechanisms for protection have been introduced in data protection legislation and such developments should always be followed by controllers and processors."
- Dr. Gabriela Zanfir-Fortuna, Senior Counsel, Future of Privacy Forum
"We have been working for several years to help organisations understand the requirements for Pseudonymisation under the GDPR with our Whitepaper on Pseudonymisation in 2017 Requirements for GDPR Compliant Pseudonymisation in 2018; and Draft Code of Conduct for GDPR Compliant Pseudonymisation in 2019. At this moment we are preparing our next steps to seek approval for our Draft Code of Conduct according to GDPR Article 40."
- Steffen Weiss, Legal Counsel Data Protection & International Affairs, Gesellschaft für Datenschutz und Datensicherheit (GDD)
"A review of the 2014 Opinion on Anonymisation is in the pipeline for the EDPB, and we are reflecting on the importance of the notion of pseudonymization as a technology-oriented way to comply with the GDPR. And this is particularly relevant in post-Schrems II."
- Giuseppe D'Acquisto, Senior Technology Advisor, Italian Data Protection Authority (Garante)
This article originally appeared in LinkedIn. All trademarks are the property of their respective owners. All rights reserved by the respective owners.
CLICK TO VIEW CURRENT NEWS[1] See Data Protection Commissioner v. Facebook Ireland Limited, Maximillian Schrems (Case C-311/18), “Schrems II”).
[2] See Memorandum to EDPB: Supplemental Measures Under Schrems II.
[4] See Next Steps for EU companies & FAQs
[5] NOYB highlights how the US uses “selectors” to surveil EU personal data. Such “selectors” may be Personally Identifying Information (PII) or direct identifiers like email addresses, IP addresses or phone numbers (“strong selectors”) or indirect identifiers like keywords or attributes that by themselves are arguably “anonymous” because they do not identify any particular person on their own, but when combined can lead to identification of individuals (“soft selectors”). See https://dcssproject.net/xkeyscore/index.html and also https://www.bbc.com/future/article/20170529-the-reasons-you-can-never-be-anonymous-again
[6] NOYB notes that “the US government has vast powers to break encryption.” This is a likely reference to capabilities like XKEYSCORE, Bullrun and Edgehill (see https://theintercept.com/2015/07/02/look-under-hood-xkeyscore/; https://en.wikipedia.org/wiki/XKeyscore; https://www.businessinsider.com/nsa-able-to-crack-encryption-thanks-to-a-simple-mistake-2015-10; https://en.wikipedia.org/wiki/Bullrun_(decryption_program); and https://www.ibtimes.com/edward-snowden-reveals-secret-decryption-programs-10-things-you-need-know-about-bullrun-edgehill.
[7] See https://noyb.eu/files/CJEU/EU-US_form_v3.pdf
[8] See Memorandum to EDPB: Supplemental Measures Under Schrems II
[9] GDPR Recital 15 states that “In order to prevent creating a serious risk of circumvention, the protection of natural persons should be technologically neutral and should not depend on the techniques used.”
[10] Examples of resources on Pseudonymisation published after the effective date of the GDPR include: (a) Recommendations on Shaping Technology According to GDPR Provisions: An Overview on Data Pseudonymisation published by The European Union Agency for Cybersecurity (ENISA) in November 2018; (b) Pseudonymisation Techniques and Best Practices: Recommendations on Shaping Technology According to Data Protection and Privacy Provisions published by ENISA in November 2019; and Draft for a Code of Conduct on the use of GDPR Compliant Pseudonymisation of the Data Protection Focus Group of the Platform Security, Protection and Trust for Society and Business at the Digital Summit 2019.
[11] See the 2016 Future of Privacy Forum (FPF) resource Visual Guide to Practical Data De-Identification which includes the correct definition of Pseudonymous Data before the GDPR: “Information from which direct identifiers have been eliminated or transformed, but indirect identifiers remain intact.”
[12] See Memorandum to EDPB: Supplemental Measures Under Schrems II