This post includes new information responding to questions raised following publication of a prior version appearing in International Association of Privacy Professionals (IAPP) Privacy Perspectives.
On January 31, I took part in an IAPP-hosted webinar on managing risk and big data analytics under the EU's General Data Protection Regulation alongside Gwendal Le Grand, the Director of Technology and Innovation at the CNIL, France's data protection authority, and Mike Hintze, former Microsoft chief privacy counsel and now partner at Hintze Law.
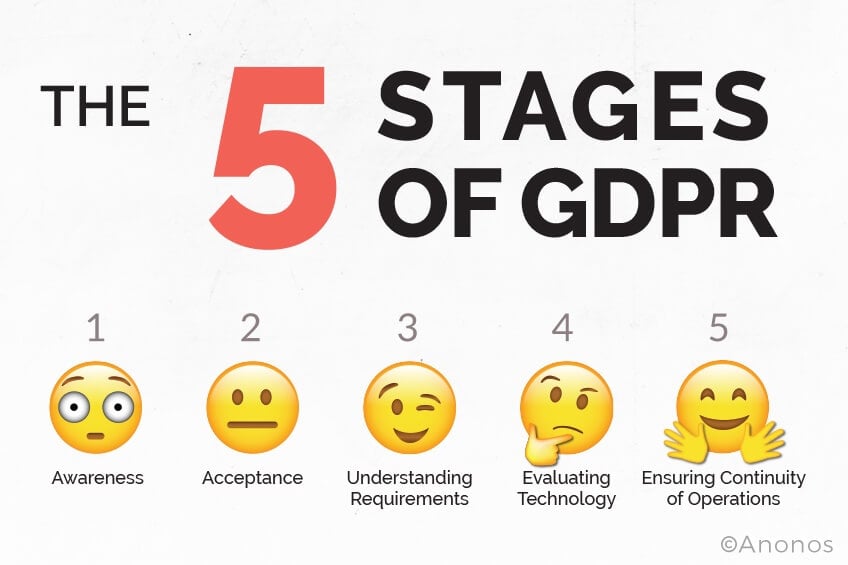
Based on interactions with companies and regulators following the webinar, we found that companies are at varying stages of adjustment to the upcoming regulation. Understanding these five stages, we believe, can help companies that control and process personal data find a solution to their needs. So, here we go:
STAGE ONE - AWARENESS
At this stage, a company is aware that the GDPR contains new protections for EU data subjects and threatens significant fines and penalties for non-compliant data controllers and processors. Since compliance enforcement commences in the spring of 2018, many companies are stuck at this stage and are postponing moving to a solution. Yet preparation for compliance with the GDPR should begin now.
The company is usually also aware of the GDPR’s broad jurisdiction. It applies to all companies processing personal data for one or more EU citizens, regardless of where the company is located or has operations. The company is also aware that penalties for noncompliance can include fines of up to four percent of global gross revenues, along with class-action lawsuits, and direct liability for both data controllers and data processors for data breaches, data breach notification obligations, and so forth.
STAGE TWO - ACCEPTANCE
A company at this stage realizes it cannot rely on prior approaches or legal bases for data analytics, artificial intelligence, or machine learning. While consent remains a lawful basis under the GDPR, the definition of consent is significantly restricted. Under the GDPR, consent must now be “freely given, specific, informed and an unambiguous indication of the data subject’s agreement to the processing of personal data relating to him or her.?
These requirements for GDPR-compliant consent are not satisfied if there is ambiguity and uncertainty of data processing, as is the case with data analytics, artificial intelligence, or machine learning, or what we'll refer to as big data henceforth. These heightened requirements for consent under the GDPR shift the risk from individual data subjects to data controllers and processors.
Prior to the GDPR, risks associated with not fully comprehending broad grants of consent were borne by individual data subjects.
Under the GDPR, broad consent no longer provides sufficient legal basis for big data. Data controllers and processors must now satisfy an alternate legal basis for big data processing.

STAGE THREE - UNDERSTANDING
At this stage, a company appreciates that the GDPR does provide a means to continue big data processing. If GDPR proportionality, necessity, and state of the art obligations are satisfied by complying with new Pseudonymisation and Data Protection by Default requirements, "legitimate interest? can be used as a legal basis for big data processing:
STAGE FOUR - EVALUATING
A company at this stage is evaluating technology to determine if it satisfies GDPR requirements for both Pseudonymisation and Data Protection by Default.
The advent of controlled linkable data
A webinar sponsored by the International Association of Privacy Professionals (IAPP), entitled How to Comply with the GDPR While Unlocking the Value of Big Data featuring Gwendal Le Grand, the Director of Technology and Innovation at La Commission Nationale de l'Informatique et des Libertés (CNIL), and Mike Hintze, former Microsoft Chief Privacy Counsel and now partner at Hintze Law, introduces the term Controlled Linkable Datat o describe new technology that achieves two critical goals:
How does Controlled Linkable Data achieve these dual goals? It replaces restricted data elements, such as personal data under the GDPR, protected health information under HIPAA, and contractually restricted elements by dynamically changing pseudonymous tokens. As a result, Controlled Linkable Data does not enable correlations or "linkage attacks" back to the identity of individuals without access to keys.
Controlled Linkable Data also provides access to more accurate data, because it unlinks it without degrading it. On the other hand, alternative approaches apply Privacy Enhancing Techniques (PETs) indiscriminately, without allowing for what purpose the data will be used for, a shortcoming that degrades the value of the data.
Controlled Linkable Data can be implemented with a revolutionary approach, called Anonos BigPrivacy. Five granted patents, plus 50+ patent applications worldwide protect the unique capability of Anonos technology to use dynamically changing identifiers to enable Controlled Linkable Data.
STAGE FIVE - ENSURING CONTINUITY
Companies at this stage of adjustment are seeking to verify that technology vendors satisfy GDPR requirements for Pseudonymisation and Data Protection by Default, so that by using the technology they can ensure ongoing continuity of operations.
At what stage are you? Let us know. Contact us.
The Anonos intellectual property program, which is backed by 5 granted patents and 50+ additional patent applications worldwide, is the only technology that assures ongoing access to dynamically changing identifiers. This assurance produces invaluable benefits:
Companies do not have to worry about disruptions in access to Anonos’ BigPrivacy implementation of Controlled Linkable Data due to claims by third parties.
Companies also have the option of using Anonos’ BigPrivacy technology the way that best suits their needs.
Note: If a vendor other than Anonos supports Pseudonymisation and Data Protection by Default, which are the two requirements for Controlled Linkable Data, by means of dynamically changing identifiers, the interested company should verify the vendor has rights under Anonos patents.
If a vendor supports Pseudonymisation and Data Protection by Default by means other than dynamically changing identifiers, the company expressing interest should verify that this alternate approach satisfies the requirements for proportionality and necessity under GDPR Recitals 4, 156, 170 and Articles 6(4), 24 and 35, as well as state of the art requirements under GDPR Recitals 78 and 83 and Articles 25 and 32.