Step #1: Your Company is Not Alone, Unless...
Your company is not alone in its desire to engage in advanced analytics, data sharing, AI, and migration to the cloud. But, data uses are evolving faster than the capabilities of traditional privacy and security controls. You must technically enforce policy controls at the data element level or your company will be left alone when competitors are maximising compliant data use, sharing and migration to the cloud.
Step #2: The Rules Have Changed...
All EU personal data effectively becomes highly regulated data under the GDPR. Many data access practices and uses which have been legal for decades will become illegal under the GDPR. Traditional privacy and security technologies do not support many lawful data uses in compliance with GDPR requirements because they cannot technically enforce policy controls at the data element level.
Step #3: May 25th is just the BEGINNING...
The “sound heard around the world” on May 25th will not be the sound of EU Data Protection Authorities imposing enormous GDPR penalties. The sound will be privacy and security teams telling technology and analytics teams that they no longer have a lawful basis to use data for advanced analytics, sharing, or AI, and that they cannot migrate data to the cloud because of the risk of these penalties. Companies are rapidly growing their data analytics teams while their privacy and compliance teams are not growing in size - only in duties and responsibilities. Privacy and compliance teams want to support business objectives, but if they can’t operationalize and automate processes many desired data uses will become illegal and no longer permitted.
Step #4: Hard to Say, Harder to Live Without…
Within the next few years, all companies will begin PSEUDONYMISING data to ensure compliant data use, sharing and migration to the cloud. Some companies are well versed in the requirements of pseudonymisation, others have a general idea of its benefits under the GDPR, and some have a hard time saying or spelling it. Pseudonymisation is very different than Anonymisation. There is no such thing as Pseudo-Anonymization. The benefits of complying with the GDPR definition of Pseudonymisation make it well worth implementing from the “edge” of data collection all the way to the data lake for streaming privacy controls. Companies that realize the benefits of pseudonymising data first will be those that leave competitors behind.
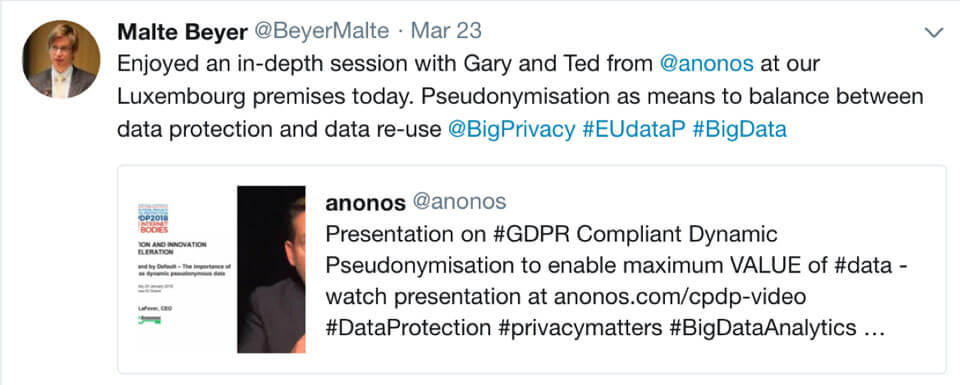
Step #5: Anonos BigPrivacy Dynamic Pseudonymisation
Data uses are getting bigger and so are privacy concerns - that is why many of the leading companies around the globe are implementing Anonos BigPrivacy dynamic pseudonymisation technology.
I had previously seen three avenues to doing data-driven innovation with personal data in a privacy compliant manner. First, you may secure the consent of a person. Second, you may find a use case where anonymized/generalized data are "just good enough," and you can prove that your method of anonymization or generalization works to prevent re-linking of data to individuals. Third, you may hope that emerging technologies for privacy-preserving analytics like multi-party computing or homomorphic encryption could help you achieve your goal. But, we have learned today that there is a new way - Anonos has introduced us to a distinct different fourth approach which is BigPrivacy dynamic pseudonymisation technology.