Use Cases & Business Applications How Anonos Data Embassy Software Mitigates
“Cloud Risk” and “Lawful Processing Risk”
Problem Statement
- The June 2021 final European Data Protection Board (EDPB) Schrems II Guidance1 clarified that only certain cloud processing remains lawful under the GDPR following the Schrems II ruling by the Court of Justice of the European Union (CJEU) on international data transfers.
- The July 2021 €746 / $887 million fine against Amazon by the Luxembourg CNPD underscored previous EDPB guidance that:

Consent
Consent is only valid as a legal basis for processing EU personal data when processing is described at the time of data collection in specific, informed and unambiguous detail so that the data subject understands what they are consenting to, and the data subject is not required to consent to the requested processing as a condition of obtaining the offered product or service, so that their consent is voluntary.2
Contract
Contract as a legal basis is to be strictly construed to cover only the minimum data processing required to support the performance of a contract. If desired processing is not strictly necessary for the performance of a contract – for example, to support advanced analytics, behavioural advertising, marketing, product improvement, profiling, etc. then Contract is not an available legal basis for processing.3
For these reasons, Consent and Contract are too restrictive to support Analytics, machine learning (ML) and artificial intelligence (AI) under the GDPR.4
This creates two significant challenges:

Cloud Risk
International data transfers were significantly impacted by the Schrems II ruling by the CJEU. Many of these issues can be addressed by enforcing technical supplementary measures recommended by the European Data Protection Board (EDPB) for lawful processing of EU personal data when using cloud-based Software-as-a-Service (SaaS), Platform-as-a-Service (PaaS), and Infrastructure-as-a-Service (IaaS) offerings of US and other third-country5 providers.

Lawful Processing Risk
The Amazon fine resulted from failure to comply with GDPR requirements for establishing a legal basis for advanced analytics undergirding targeted advertising. These matters can be largely addressed by enforcing technical and organizational safeguards to satisfy the requirements for the GDPR legal basis of Legitimate Interests processing by mitigating the risks of the processing to data subjects’ rights and freedoms.6
Prerequisites for Anonos Use Cases
Organisations should verify that:
They have a lawful basis under Article 6 of the GDPR for the initial collection of EU personal data.
For data not collected and stored in the EU, they satisfy the requirements for a derogation8 or a recognised EDPB use case relative to international transfers for storing the data.9
Note: this is a separate, additional requirement beyond having a lawful basis for the initial collection of EU personal data.
Note: this is a separate, additional requirement beyond having a lawful basis for the initial collection of EU personal data.
Irrespective of location, the desired further processing is compatible with the original purpose.10
Anonos
use case one
use case one
Mitigating Cloud Risk
The data controller uses Anonos Data Embassy software to create state-of-the-art GDPR compliant Pseudonymisation-enabled Variant Twins® from the desired data, which must be in the EU at the time of transformation, which are then uploaded to the cloud or otherwise transferred internationally to a third country for processing in compliance with Schrems II obligations. Anonos Variant Twins satisfy the requirements of EDPB final Schrems II Use Case 2: Transfer of Pseudonymised Data11 because they are “surveillance proof”: they are non-identifiable personal data that cannot be re-linked to identity without access to “additional information” that is kept separately by the EU controller.12
Using Anonos Variant Twins, a data controller can establish by default the processing of protected Pseudonymised data whenever, wherever, as often as possible. The data controller processes identifying data, or uses the “additional information” held separately to relink results of Variant Twin processing to EU data subject identities, only when necessary, and provided that:
Using Anonos Variant Twins, a data controller can establish by default the processing of protected Pseudonymised data whenever, wherever, as often as possible. The data controller processes identifying data, or uses the “additional information” held separately to relink results of Variant Twin processing to EU data subject identities, only when necessary, and provided that:
- There is a legal basis to do so under Article 6 (e.g., based on Article 6(1)(a) Consent, 6(1)(b) Contract, or 6(1)(f) Legitimate Interests13); and
- The processing satisfies derogation requirements (e.g., Article 49(1)(a) based on consent, Articles 49(1)(b) or (c) based on contract);14 or
- The processing is localised within the EEA or EU Equivalency Countries. Note that the GDPR mandatory obligations to implement technical and organizational controls that enforce the principles relating to processing of personal data, data protection by design and default, and security of processing still apply.15
Anonos’ patented Variant Twin software leverages GDPR-compliant Pseudonymisation, leveraging advanced, scalable dynamism capabilities to mitigate the risk of re-identification, reconciling tensions between data innovation and increasingly stringent requirements for ethical and lawful processing. In addition, Variant Twins enforce data element-level controls to support GDPR-compliant Pseudonymisation to satisfy the Balancing of Interest test required for valid Legitimate Interests processing under the GDPR.16
With Anonos Variant Twins, the protection is embedded into the data in such a way that the benefits of combining ever-increasing sources of data remain, but in a privacy respectful, lawful manner.
Best of all, Variant Twins enable lawful data sharing, combining, analytics, AI and ML without degrading the accuracy or speed of processing compared to cleartext data.17
With Anonos Variant Twins, the protection is embedded into the data in such a way that the benefits of combining ever-increasing sources of data remain, but in a privacy respectful, lawful manner.
Best of all, Variant Twins enable lawful data sharing, combining, analytics, AI and ML without degrading the accuracy or speed of processing compared to cleartext data.17
Anonos
use case Two
use case Two
Mitigating Lawful Processing Risk
Business Applications of Anonos Use Cases
The following business applications highlight numerous examples of some of the benefits from transforming current business practices involving the processing of vulnerable identifying cleartext data – which is not required to produce the desired results – to processing protected GDPR Pseudonymised data whenever, wherever, as often as possible. When using Anonos Data Embassy GDPR Pseudonymisation-compliant software, identifying cleartext data is used only when lawful derogations (i.e., exceptions to prohibitions) exist.
1
BI reporting Using Cloud-Based Applications
Anonos Data Embassy software enables GDPR Pseudonymisation of direct and indirect identifiers and attributes to create pivot tables representing personal data before the information is used for BI processing hosted on US cloud platforms, regardless of the location of the servers. This enables processing in compliance with both Schrems II and GDPR legal basis requirements. When someone wants to “drill down” to see identifying data, Variant Twins can be used by a data controller in the EU to relink to identifying data to provide the desired details.
2
E-mail Marketing Campaigns
Variant Twins are created that pseudonymise all personal data in compliance with heightened GDPR requirements for each individual, which are then processed against cleartext non-personal data that serve as filtering criteria. After Variant Twins representing the people desired in outreach are determined, the identities represented by the Variant Twins are compared against Variant Twins representing customers (i) who have opted out of receiving offers or (ii) are already involved in campaigns, thereby avoiding contacting people who should not receive offers. Once the Variant Twins representing the people who should receive offers are identified, the data controller can use the “additional information” held separately to relink the results of the Variant Twin processing to EU data subject identities provided that (i) there is a legal basis to do so under Article 6, and (ii) processing satisfies derogation requirements.
This approach protects personal data until data subjects’ email addresses are needed to transmit offers to them individually. It is important to note that restricting the use of email services to EEA/Equivalency Country providers will not improve privacy since data travels across the internet in packets. When an e-mail is sent, the message breaks up into packets that travel across the global Internet Protocol (IP) network. Different packets from the same message don't necessarily follow the same path. Rather, packets travel from one machine to another until they reach their final destination, with the processing occurring in milliseconds. The computer finally receiving the data assembles the packets like a puzzle, recreating the message. This differs from a phone system that creates a dedicated circuit through a series of switches, but which are susceptible to failure if something happens to the connection. In contrast, if a connection in the IP network should fail, data can travel across an alternate route. As a result, there's no guarantee that an email sent from Paris to Madrid does not process on routers in the US or another third country.
This approach protects personal data until data subjects’ email addresses are needed to transmit offers to them individually. It is important to note that restricting the use of email services to EEA/Equivalency Country providers will not improve privacy since data travels across the internet in packets. When an e-mail is sent, the message breaks up into packets that travel across the global Internet Protocol (IP) network. Different packets from the same message don't necessarily follow the same path. Rather, packets travel from one machine to another until they reach their final destination, with the processing occurring in milliseconds. The computer finally receiving the data assembles the packets like a puzzle, recreating the message. This differs from a phone system that creates a dedicated circuit through a series of switches, but which are susceptible to failure if something happens to the connection. In contrast, if a connection in the IP network should fail, data can travel across an alternate route. As a result, there's no guarantee that an email sent from Paris to Madrid does not process on routers in the US or another third country.
3
Cybersecurity/Fraud Detection
Cybersecurity and fraud experts rely on monitoring global source data to identify anomalous behaviour that, in some instances, represents bad actors. These data sets are some of the most sensitive data any company holds. Being able to create privacy preserving views of the data enables data science teams and models to evaluate risk in new ways with greater scale to identify bad actors. By providing detection models with Variant Twins representing personal data to enable identification of outlying values with suspicious “signals” in them, EU data controllers can use the suspicious Variant Twins to identify source data only when there is a record that needs to be investigated, provided that (i) there is a legal basis to do so under Article 6, and (ii) processing satisfies derogation requirements or is localised within the EEA or Equivalency Countries.
4
Access to Outsourced Expertise
Organisations desire to outsource processing – via cloud or remote access arrangements – when they don't have the internal resources to perform them internally. In these instances, Variant Twins can be created that reflect discrete but sufficiently large groups reflecting homogenous characteristics, behaviours, etc., to enable analysis without revealing identities. This enables compliance with both Schrems II and GDPR legal basis requirements. When identifying data is desired, Variant Twins can be used by a data controller in the EU to relink to identifying data to provide the desired details. Examples of this business application include Marketing Automation (in the form of Lead Prospecting, Lead Identification, Upsells or Cross-Sells, and Conversion); Advanced Analytics, ML and AI; and Follow-the-sun (24X7) processing or support.
5
Multi-Organisation Coordinated Activities
Anonos Data Embassy software enables the evaluation of overlap or complement between and among different data sets at a non-identifying but information-rich level by creating Variant Twins that reflect discrete but sufficiently large groups (Microsegments) reflecting homogenous characteristics, behaviours, etc., to enable analysis without revealing identities. Examples of potential multi-organisation coordinated activities include potential combinations, mergers and acquisitions, joint ventures, coordinated marketing campaigns, etc. Organisations can compare data sets without revealing personal data to determine if there is sufficient rationale to justify coordinated activities, provided that (i) there is a legal basis to do so under Article 6, and (ii) the activity satisfies derogation requirements or is localised within the EEA or Equivalency Countries.
6
Talent Analytics
HR data is used for many purposes, some of which are addressable using Anonos Data Embassy enabled GDPR Pseudonymisation. For example, Anonos Variant Twins may be used to support Talent Analytics by enabling the evaluation of patterns among groups of people that are homogeneous enough to reflect unique attributes or behaviours or capabilities but large enough that they don’t reveal individual identities. The individuals represented by each Variant Twin may then be disclosed provided (i) there is a legal basis to do so under GDPR Article 6, and (ii) the processing satisfies derogation requirements or is localised within the EEA or Equivalency Countries.
7
Third-Party Evaluation
Anonos enables companies to build protected Variant Twin versions of data assets for privacy-preserving sharing with third parties in a private and compliant manner so that machine learning & artificial intelligence code, outsourced risk models, algorithms, software and other data-driven products can be evaluated to make timely decisions on licensing, investment or acquisition.
An example of Third-Party Evaluation is “API monetization,” involving generating revenues from using APIs. APIs are an iteration of business development, where having well-developed APIs establishes and maintains relationships in a digital economy. Having private and compliant Variant Twin versions of data assets available for API’s provides maximum value when considering New Data Economy opportunities.
An example of Third-Party Evaluation is “API monetization,” involving generating revenues from using APIs. APIs are an iteration of business development, where having well-developed APIs establishes and maintains relationships in a digital economy. Having private and compliant Variant Twin versions of data assets available for API’s provides maximum value when considering New Data Economy opportunities.
8
Business Continuity for US Data Flows
Increasingly, US state privacy laws (e.g., California, Colorado, and Virginia) require the deletion of identifying data from both an organisation’s systems as well as all third parties to whom data was shared, in response to “do not sell my data requests.” However, these laws include exceptions for properly transformed versions of data in compliance with statutory requirements for protection, which are satisfied using Anonos Data Embassy software.
9
Transform Economies
Transform local and global economies by leveraging Fourth Industrial Revolution (4IR) technologies to reimagine consent and permission mechanisms differently. See World Economic Forum article Data marketplaces can transform economies. Here’s how.18
10
Avoid Criminal and Personal Liability
Section 171 of the UK version of the GDPR makes it a criminal offence to knowingly or recklessly re-identify information that is de-identified without permission. Section 198 provides that executives and Board members can be found personally liable for failing to comply with data protection requirements “by consent, connivance, or … neglect.” Compliance with Data Protection by Design and by Default obligations under Article 25 and Security obligations under Article 32 using GDPR Pseudonymisation helps establish the standard of care necessary to avoid liability.
11
Synthetic Data Replacement
Organizations have historically used synthetic data for many leading data use cases, but with limitations. Synthetic data can't be joined with other data sets, so for each iteration of the data journey new synthetic datasets have to be generated. This slows down and restricts the analytical generation process. Also, by definition, synthetic data is not real so you can never create actionable insights at an individual record level. Creating a Variant Twin with Data Embassy software to a defined level of protection can replace the synthetic data and create protected assets that can be combined, modeled, or enriched but still hold the ability to deliver granular actionable insights.
References
- See EDPB Guidelines at https://edpb.europa.eu/system/files/2021-06/edpb_recommendations_202001vo.2.0_supplementarymeasurestransferstools_en.pdf
- See EDPB Guidelines 5/2020 at https://edpb.europa.eu/sites/default/files/files/file1/edpb_guidelines_202005_consent_en.pdf
- See EDPB Guidelines 2/2019 at https://edpb.europa.eu/sites/default/files/files/file1/edpb_guidelines-art_6-1-b-adopted_after_public_consultation_en.pdf
- As made clear in the case filed by Privacy International against Acxiom and Oracle (data brokers), Equifax and Experian (credit reference agencies), and Criteo, Quantcast and Tapad (ad-tech companies) with data protection authorities in France, Ireland, and the UK. See https://privacyinternational.org/advocacy/2434/why-weve-filed-complaints-against-companies-most-people-have-never-heard-and-what
- Third countries are those that are not members of the European Economic Area (EEA) or which have not received an EU Adequacy Decision. Processing EU personal data using SaaS, PaaS or IaaS services provided by organisations organised, directly or indirectly, under the laws of the US or other third countries is considered international data transfer, regardless of the physical location of the servers on which processing occurs, due to the potential access to such data by third country government agencies.
- The Legitimate Interests legal basis reflects the GDPR’s risk-based approach to enabling the processing of personal data when it does not result in a risk of harm to data subjects. However, it is not enough to assert a legitimate interest in the results of the processing; the legal basis “cannot be equated to the interest of companies to making a profit from personal data." (See Supra, Note 3). The EDPB notes that the Legitimate Interests legal basis (See Article 29 Working Party Opinion on the notion of legitimate interest of the data controller under Article 7 of Directive 95/46/EC, currently under revision by the EDPB (see the EDPB Work program 2021/2022 adopted on the 16 March 2021) requires a controller to satisfy three conditions: (1) Legitimate Interest: the identification and qualification of a legitimate interest pursued by the controller or by a third party; this interest of the controller or third party may be broader than the purpose of the processing but must be present on the processing date; (2) Necessity: the need to process the personal data must be established as a requirement for the legitimate interest pursued; and (3) Balancing of Interests: the legitimate interest of the controller or third party must be balanced against the interests or fundamental rights and freedoms of the data subject, including the data subject's rights to data protection and privacy, considering the particular circumstances of the processing. GDPR Pseudonymisation is recognised as a means of “tipping the balance in favour of Legitimate Interests processing.” See Articles 5(1)(a), 6(1)(f), and Opinion 06/2014 on the notion of legitimate interests of the data controller at https://ec.europa.eu/justice/article-29/documentation/opinion-recommendation/files/2014/wp217_en.pdf.
- See https://www.linkedin.com/pulse/identifying-data-maybe-unlawful-gdpr-pseudonymisation-magali-feys/
- See EDPB Guidelines at https://edpb.europa.eu/sites/default/files/files/file1/edpb_guidelines_2_2018_derogations_en.pdf
- See Supra, Note 1, at Paragraph 84 Use Case 1: Data storage for backup and other purposes that do not require access to data in the clear, and Paragraph 90 Use Case 3; Encryption of data to protect it from access by the public authorities of the third country of the importer when it transits between the exporter and its importer.
- GDPR Pseudonymisation-enabled functional separation of personal data (using technical and organisational safeguards to separate information value from identity to enable the discovery of trends and correlations independent from applying the insights gained to the data subjects concerned) helps organisations to ensure that secondary processing is “compatible” with the original purpose. Under the GDPR, when an organisation processes personal data obtained for a particular permitted purpose, it cannot process it further except for purposes that are compatible. (See GDPR Article 5(1)(b)). Further processing data may be deemed compatible with the original purpose if the processing satisfies the requirements of either (i) GDPR Article 6(4) with respect to further “processing for a purpose other than that for which the personal data have been collected…not based on the data subject’s consent”; or (ii) Article 89(1) with respect to processing conducted for “archiving purposes in the public interest,” “scientific or historical research purposes,” or “statistical purposes.” Pseudonymisation is explicitly‑recognised as a safeguard under Article 6(4)(e) to help ensure that any further processing of personal data “is compatible with the purpose for which the personal data are initially collected” in compliance with Article 5(1)(b) (“purpose limitation”) requirements. Under Article 89(1) further processing for “archiving purposes in the public interest,” “scientific or historical research purposes,” or “statistical purposes” is specifically considered not to be incompatible with the initial purposes if appropriate safeguards for data subjects are provided to ensure, in particular, data minimisation, and such measures explicitly include Pseudonymisation.
- See Note 1, at Paragraph 85 Use Case 2: Transfer of pseudonymised Data.
- Gartner Group recognises Anonos as a Gartner Cool Vendor because patented “Variant Twins” create controllably re-linkable yet non-identifiable data sets from personalised data. See https://www.anonos.com/awards.
- See Note 7.
- See Note 9.
- See GDPR Articles 5, 25 and 32 and Note 1, at Paragraphs 76 and 83.
- See Note 7.
- See https://www.anonos.com/data-scientist-expert-opinion
- See https://www.weforum.org/agenda/2021/08/data-marketplaces-can-transform-economies/
Appendix
Technology Comparison for Maximum Data Value at Scale
Anonos Data Embassy state-of-the-art GDPR Pseudonymisation-compliant software achieves “Aristotle’s Golden Mean” of balancing between two extremes: maximum data value and protection. GDPR Pseudonymisation is the most misunderstood and underutilised means of simultaneous data enablement and protection. With Anonos patented Data Embassy software, organisations no longer need to engage in high-risk unlawful processing of data in the clear to achieve 100% accurate data innovation to accomplish business objectives.
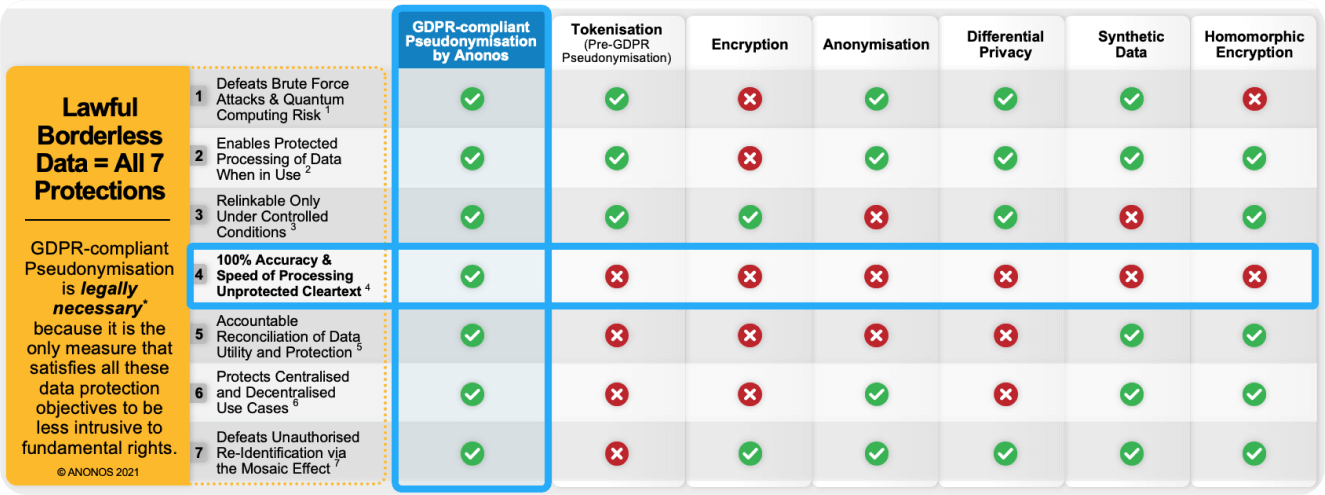
* Pseudonymisation is “legally necessary” under EU law when it is less intrusive to and more protective of rights under the GDPR and the EU Charter of Fundamental Human Rights than other data protection techniques. See European Court of Justice (ECJ) Case C-362/14, Schrems v. Data Protection Commissioner (October 2015 – “Schrems I”), and ECJ Case C‑311/18, Data Protection Commissioner v Facebook Ireland Limited and Maximillian Schrems (July 2020 – “Schrems II”).
- EDPB Final Guidance paragraphs 83 and 89 and footnotes 80 and 81.
- EDPB Final Guidance executive summary “...the protection granted to personal data in the European Economic Area (EEA) must travel with the data wherever it goes.”
- EDPB Final Guidance paragraphs 85, 94 and 96.
- GDPR Article 5(1)(d). See also www.anonos.com/data-scientist-expert-opinion.
- EDPB Final Guidance paragraphs 3, 4, 5 and 67.
- EDPB Final Guidance executive summary “...the protection granted to personal data in the European Economic Area (EEA) must travel with the data wherever it goes.”
- EDPB Final Guidance paragraphs 79, 85, 86, 87, 88. See also https://www.MosaicEffect.com/
Anonos GDPR Pseudonymisation is State-of-the-Art
GDPR Pseudonymisation is the state-of-the-art[1] for protecting data when in use while ensuring accuracy. [2] When implemented in compliance with GDPR Article 4(5) definitional requirements, pseudonymisation protects direct and indirect identifiers and attributes at the record/data set level (not just at the field level) making use of non-algorithmic derived look-up tables. If the data is to be used in multiple data sets, different tables/tokens are used at different times for various purposes (i.e., dynamism) to prevent correlations among data sets that could lead to unauthorised reidentification.[3] Only by using “additional information held separately,” can data pseudonymised to GDPR standards be relinked to the identity of data subjects enabling maximum accuracy for authorised processing.
Anonos Data Embassy[4] software is the result of over 8 years and tens of thousands of hours of legal and technical research and development. The commitment by Anonos to inventing and implementing state-of-the-art technology for reconciling conflicts between data security, protection and innovation is evidenced by the following achievements:
Anonos Data Embassy[4] software is the result of over 8 years and tens of thousands of hours of legal and technical research and development. The commitment by Anonos to inventing and implementing state-of-the-art technology for reconciling conflicts between data security, protection and innovation is evidenced by the following achievements:
- Anonos technology is the only technology certified as complying with GDPR Pseudonymisation requirements.[5]
- Anonos “Best Practices” for Schrems II compliant transfers are included in the Code of Conduct for Pseudonymisation submitted to the EDPB by the German Association for Data Protection and Data Security (“GDD” or Gesellschaft für Datenschutz und Datensicherheit e.V.).[6]
- Anonos Data Embassy software complies with all 50 of the GDPR-compliant Pseudonymisation Best Practices derived by Anonos after careful study and analysis of three reports by the European Union Agency for Cybersecurity (ENISA).[7]

Anonymisation
Anonymisation is not the state-of-the-art for protecting data when in use because of the availability of external data sets for augmenting purportedly anonymised data enabling unauthorised reidentification.[8]
Differential Privacy
Differential Privacy is not the state-of-the-art for protecting data when in use because it: (i) is a “zero sum game” involving an inherent tradeoff between accuracy and privacy; and (ii) requires processing within restricted parameters to manage a “privacy budget” by controlling the data, use cases and users involved.
Encryption
Encryption is not the state-of-the-art for protecting data when in use because it: (i) protects data only when it is in storage and in transit and not when it is in use; and (ii) is susceptible to brute force attacks and quantum computing risk. While Homomorphic Encryption (HE) protects data when in use, (i) it requires changes to existing Analytics, AI and ML applications, (ii) its high computational overhead and elapsed processing requirements are impracticable for many applications, and (iii) the delays from extended processing cycles, in time-sensitive situations, may produce results that are no longer accurate, relevant, or actionable.
Multi-Party Computing (MPC)
MPC is not the state-of-the-art for protecting data when in use because: (i) it requires changes to existing Analytics, AI and ML applications; (ii) its high communication demands, computational overhead and elapsed processing requirements are impracticable for many applications, and (iii) the delays from extended processing cycles, in time-sensitive situations, may produce results that are no longer accurate, relevant, or actionable.
Synthetic Data:
Synthetic Data is not the state-of-the-art for protecting data when in use because it: (i) provides less than 100% precision; (ii) does not enable relinking to identity for authorised processing; and (iii) requires recalibration each time the composition of source data changes.
Appendix References
[1] The GDPR requires that parties (i) use the state of the art in complying with GDPR obligations or (ii) if not, to document why they are not doing so. This obligation to use the state of the art is specifically tied to complying with the newly heightened requirements for GDPR Pseudonymisation as a critical element of both Data Protection by Design and by Default (Article 25) and Security of Processing (Article 32).
[2] Article 5(1)(d) provides that personal data must be “accurate and, where necessary, kept up to date; every reasonable step must be taken to ensure that personal data that are inaccurate, having regard to the purposes for which they are processed, are erased or rectified without delay.” GDPR Pseudonymisation is state-of-the-art for protecting data when in use while ensuring accuracy. When implemented in compliance with GDPR Article 4(5) definitional requirements, pseudonymisation protects direct and indirect identifiers and attributes at the record/data set level (not just at the field level) making use of non-algorithmic derived look-up tables. If the data is to be used in multiple data sets, different tables/tokens are used at different times for various purposes (i.e., dynamism) to prevent correlations among data sets that could lead to unauthorised reidentification (see https://www.MosaicEffect.com). Only by using “additional information held separately,” can data pseudonymised to GDPR standards be relinked to the identity of data subjects enabling maximum accuracy for authorised processing.
[3] See https://www.MosaicEffect.com.
[4] The capabilities of Anonos software, previously branded as “Big Privacy”, to satisfy GDPR and Schrems II requirements are highlighted in an IDC report titled “Embedding Privacy and Trust Into Data Analytics Through Pseudonymisation,” available at https://www.anonos.com/hubfs/Embedding_Trust_Into_Data_Anonos_IDC_August_2020.pdf. Anonos changed the name of its software from “Big Privacy” to “Data Embassy” because when travelling in a foreign country, travelers can turn to their home country’s embassy for predictable protection and physical security. Anonos reasoned that similarly, its Data Embassy software embeds protection and physical security into data no matter “where it travels” or what country it is in.
[6] See www.Anonos.com/TenTruths
[7] See https://www.enisaguidelines.com/
[8] See footnote 2 in Annex II COMMISSION IMPLEMENTING DECISION (EU) 2021/914 at https://eur-lex.europa.eu/legal-content/EN/TXT/PDF/?uri=CELEX:32021D0914&from=EN which stipulates that anonymisation “requires rendering the data anonymous in such a way that the individual is no longer identifiable by anyone, in line with recital 26 of Regulation (EU) 2016/679, and that this process is irreversible.” The EDPB highlights that the availability of external data sets enabling unauthorised reidentification must be considered. See paragraphs 79, 85, 86, 87, 88 of Recommendations 01/2020 on Measures that Supplement Transfer Tools to Ensure Compliance with the EU Level of Protection of Personal Data https://edpb.europa.eu/system/files/2021-06/edpb_recommendations_202001vo.2.0_supplementarymeasurestransferstools_en.pdf. See also https://www.MosaicEffect.com.
SEE WHAT OTHERS HAVE TO SAY ABOUT US

Anonos’ technology allows for re-linkable non-identifying personalized data and shows how advances in technology makes our ability to leverage data for better outcomes plausible today.
Anonos is cool because its patented technology creates re-linkable non-identifying personalized data called Variant Twins that enable compliant analytics, ML, AI and data sharing.
The added value from the Anonos solution is that we can share insights with intergroup entities, by only sharing the insights and not the identity behind the insights. This allows innovative cooperation, and no problems with the GDPR.
We believe Anonos is well-positioned with its state-of the-art pseudonymisation capabilities and granular protection control settings to capitalize on demand for privacy-preserving data analytics.
Anonos technology enables technical enforcement of policies to break apart the silos that plague companies, allowing knowledge transfer in a privacy-respectful yet information-rich manner.
Anonos is more than GDPR compliance technology. It engineers privacy into solutions to enable lawful analytics and big data.
© 2024 Anonos. All rights reserved. Privacy Policy