November 2, 2022
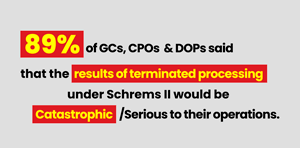
Azowo raises 10 million - Orderlion gets 4 million - Anonos acquires Statice (A)
Der #DealMonitor, unsere Übersicht über Investments und Exits, bietet werktäglich alle Deals des Tages. Heute geht es um Azowo, Orderlion, Flowers, ReDev, Anonos, Statice, Event Inc, Aloom, Inspiratie Op Locatie und Savd.
Read more