Slide 12
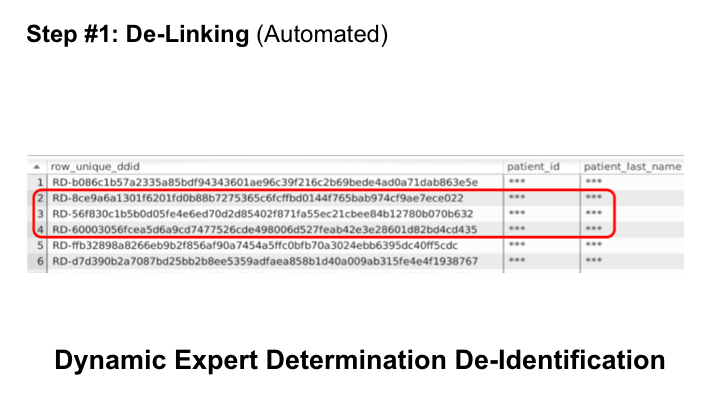
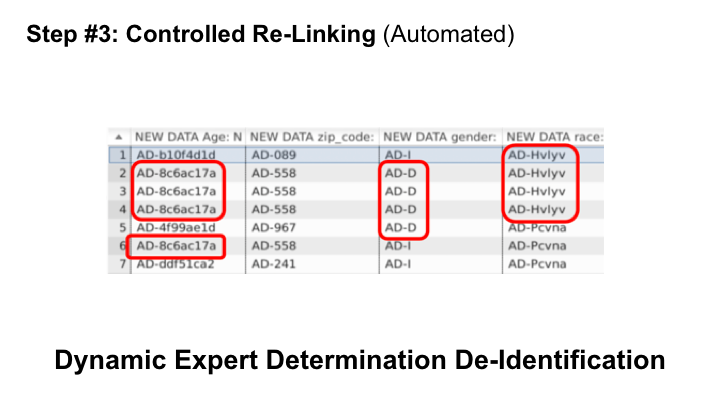
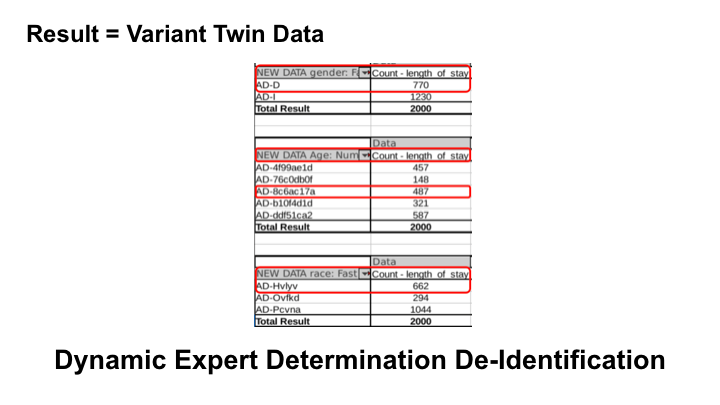
In the third step, BigPrivacy dynamically classifies values within cohort classes for later controlled re-linking. In this example, age, gender, and race are represented by cohorts that do not reveal underlying values to protect against discrimination.